Always exercise extreme caution when using publicly posted onion URLs. If you can’t get a personal recommendation from someone you trust, verify the URL from multiple sources. As long as users take the necessary precautions, no one knows who anyone else is in the real world. Users’ identities are safe from the prying eyes of governments and corporations. The dark web, or dark net, is a small part of the deep web that is kept hidden on purpose. Websites and data on the dark web do typically require a special tool to access.
Why Use The Reddit Darknet Market List 2024?
Successfully navigating this hidden world requires preparation, vigilance, and a thorough understanding of both the technical and ethical challenges at play. From choosing the right networks and privacy tools to avoiding scams and malicious software, every step you take should be guided by caution and informed judgment. Navigating the Dark Web can be a complex endeavor, but you don’t have to do it alone.
Types Of Dark Web Websites
Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI.
How Do I Verify Onion Links?
Reputable organizations, security researchers, and privacy advocates provide a wealth of insights, tutorials, and software to help you explore safely and responsibly. Below are some trustworthy starting points and authoritative references. Keep in mind that those links won’t work unless you’re accessing the Darknet through the Tor Browser.

Search Code, Repositories, Users, Issues, Pull Requests
- However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces.
- Setting up I2P requires more configuration on the user’s part than Tor.
- It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications.
- Moreover, it’s not only the entertainment industry that gets hit; some sell cracked versions of the most expensive software, and others offer pirated eBooks and academic material at cheap prices.
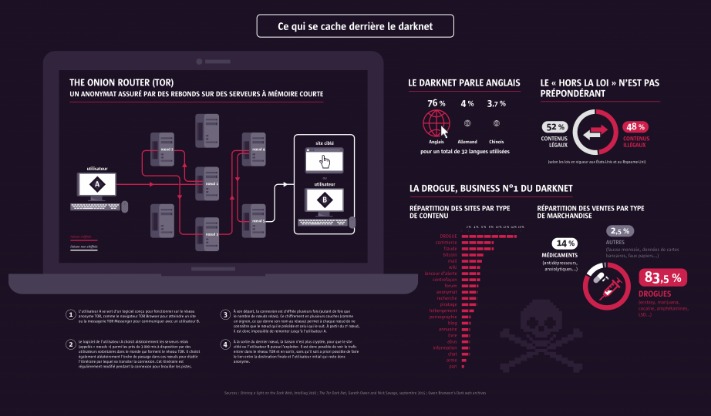
However, it didn’t close the chapter on the dark web but, instead, opened the gates for many imitation sites. The subsequent captures of dark web operators resulted in a constant cat-and-mouse game, further embedding the idea of lifestyle communities within the web’s shadows. A pivotal moment in the history of the dark web came in 2002 with the introduction of Tor (The Onion Router). Naval Research Laboratory, Tor utilized layered encryption to shield sources and destinations of internet traffic. As Tor gained traction, users flocked to it, enabling them to navigate the internet outside the boundaries of traditional scrutiny.

Mgm Grand Market
As the title suggests, it discusses cybercrime and the dark web, but in two different sections. The first section deals with cybercrime and explores some of the most famous leaks, DDoS attacks, and the deployment of viruses or worms. Archetyp Market stands out for its user-friendly interface and diverse product range.
Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website. There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information. Then, simply click the operating system that you are using and download the file. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store.
What Can I Do If My Personal Information Is On The Dark Web?
You can use dark web monitoring services or free tools like haveibeenpwned.com to check if your email, passwords, or other personal data have appeared in known dark web data breaches or dumps. ⚠️ Unfortunately, once your data appears on the dark web, there’s no reliable way to erase it. Several secure email providers, such as Riseup and Mailbox.org, provide onion sites for users who want to add an extra layer of privacy and anonymity to email communications. Tor is an entire network (not just a browser) of volunteer-run servers, known as nodes or relays, that work together to hide online activity.

Which Darknet Markets Accept Zcash
- As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor.
- What made his character interesting was using the dark web to build a powerful and ruthless cartel that survived law enforcement onslaught for years.
- Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet.
- Tor helps mask their location and Internet traffic through multiple layers of encryption, making it exceedingly difficult for malicious actors or authorities to track them.
- As stated earlier, neither of these connected content repository networks are illegal to access.
The deep web includes any online content that lives behind a login screen, paywall or other access restriction and therefore remains invisible to search‑engine crawlers. Corporate intranets, subscription databases, academic journals and your personal cloud storage all reside here. Although the term may sound ominous, most deep‑web activity is mundane and perfectly legal. For instance, when you sign in to your bank’s website to review recent transactions, you are operating within the deep web. The pages exist on standard servers, but their privacy controls prevent public indexing, keeping sensitive data out of search results. The dealer trend is helped by the fact that drugs on the darknet are both cheaper and more potent than what is available on the street.
With its expanding vendor base, the market boasts an impressive selection of unique and exceptional items, offering more than the usual darknet fare. The sad reality is the fact that law enforcement agencies can’t track and prosecute perpetrators or even take down such content given the anonymous nature of the dark web. As much as authorities work hard to shut down various sites, it shows what the dark web is capable of doing if left unchecked. That’s exactly what happens when it comes to the dark web marketplaces.

Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. In 2002 the dark web began to grow significantly when researchers backed by the U.S.
In today’s climate, where data breaches and invasive surveillance have become commonplace, understanding how to access the Dark Web and its underlying technologies is becoming increasingly relevant. Whether you’re exploring it out of curiosity or for legitimate personal reasons, it’s essential to approach this hidden realm with the right knowledge, tools, and security measures. Privacy and security are essential concerns when surfing the dark web.



