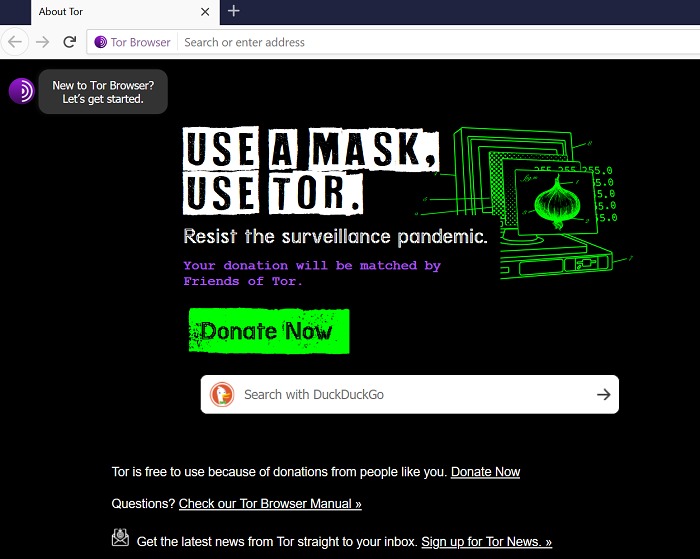
It is a complete operating system dedicated to advanced security and anonymity. Whonix combines the Tor network, a Kicksecure Hardened core, and the security by isolation principle for a comprehensive privacy solution. Although the dark web is rumored to be hard to access, the Tor Browser is just a quick install away. With Tor installed on your PC or mobile phone, you’ll be able to browse active onion websites and protect your online privacy and anonymity. While getting in isn’t that difficult, doing so safely does require following some basic steps—especially if you want to keep your privacy intact.
We Helped Patch A Chromium Bug That Could Leak Your Real IP — Here’s How
While we’re talking about Tor, here’s how to use Tor on your Chromebook. While VPN over Tor is a bit more complicated to set up, it protects you against malicious exit nodes. All data is routed from the exit node through a secure VPN connection. This prevents the node operator from detecting your IP address or from finding out any other information.
Method II – VPN Over Tor
So, even though it does exist on the internet, Google doesn’t index any of these pages or content. Google considers the majority of the content on the entire web highly irrelevant and useless to its users. That’s why such a large percentage (as much as 94%) of the entire web is not returned in Google Search. In this article, we have listed all the top 5 best Dark web Browsers to surf the web anonymously and to stay secure online.
How To Set Your Default Browser On Any Device
- The Amnestic Incognito Live (TAILS) is a live OS developed to offer complete anonymity and privacy for users.
- Before diving into how these browsers function or which ones are worth your trust in 2025, it’s important first to understand what dark web browsers actually are.
- Haystak is used to search dark web marketplaces, leaked databases, and darknet forums, often by cybersecurity experts.
- Do not attempt to download anything from the dark web as it may contain malware.
- This was also Google’s latest official update on how many pages are in their database.
Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web.
Protect Your Online Privacy With AVG Secure VPN

It contains millions of scientific research documents from around the world. The site seeks to liberate information by making it free to individuals and institutions. The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. Moreover, due to its popularity, many copycats of the Hidden Wiki exist.
#4 – Firefox
Although the underground internet world is rife with everything bad, it also hosts positive elements. It then depends on you, as the user, how you surf the dark world. We hope that this article on deep web browsers helped you by providing a long list of options that you can download and use to access the second layer of the internet, i.e Deep Web.
How To Access The Dark Web Using Tor
Additionally, you can opt for Subgraph OS as a second option to Tor. Be sure that your experience with Whonix will be comparable to Tor because both programs share the same source code. These sites aren’t just important resources; they’re like lifelines used to serve readers living under oppressive regimes. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged.
Awazon Market Link And Access Guide 2025
While Tor may be the most popular hidden web browser, the Tails system is, in fact, one of the best. This is easily one of the most popular dark web browsers currently available, and well worth looking into if you’re looking for a safe and fast dark web experience. Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Hackers know that Tor is full of curious and unsuspecting users, and have laid many traps with viruses and malware. Though Tor assigns exit nodes randomly, anyone can register to be an exit node because the process for node registration is not well-regulated.
How To Stop Pop-Up Ads On Android Phones
While Tor offers strong privacy protections, it comes with notable drawbacks that can make it impractical for everyday use, and the dark web content it grants access to can put users at risk. Please note that while using and browsing the Tor network is not illegal, it is possible to find yourself engaged in illegal activities while online. We do not condone nor encourage you to engage in these activities, and you do so at your own risk. In an era where our smartphones are an extension of ourselves, the GPS (Global Positioning System) plays a pivotal role in navigating daily activities. From checking in at your favorite spots on social media to accessing region-specific content or even for security purposes, your phone’s GPS location can be quite revealing. However, there might be instances where you want to bypass geographical constraints.
No accidental leaks if your connection drops, just a hard shutdown until you reconnect. NordVPN runs on AES-256 and ChaCha20 encryption, has a no-logs policy independently audited by Deloitte, and offers obfuscated servers for countries that block Tor or VPN use altogether. We stress-tested it using Tor over VPN, then flipped it and ran VPN over Tor, both held up without any weird breaks or traceable info. We tested them with Tor, hit multiple .onion sites, and didn’t flinch.
- The users of the dark web are typically aiming to block governments from snooping on them.
- Never put your personal info into an HTTP site, whether it’s in Tor or on the surface web.
- It’s important to choose the best VPN based on a few key points.
- Through the use of onion routing and many layers of encryption to conceal users’ names and locations, darknets provide secret and anonymous communication.
- Tor, short for “The Onion Routing project,” is a free, open-source network built to protect online privacy and enable access to the dark web.
Top Dark Web Browsers
Dark web browsers are a special type of browser designed to access websites that aren’t available on the regular internet and can’t be accessed using regular browsers like Safari, Chrome, or Firefox. These websites often use the .onion domain and are hidden from traditional search engines like Google or Bing. Within this network, the dark web represents an even more secluded sector, where access not only requires knowledge but also specific protection measures.
Users should be well aware of these risks before venturing into this part of the internet. Upon visiting the official download page and selecting the macOS option, a disk image (.dmg) file will be downloaded. After the download, the user needs to open the .dmg file, which will mount a virtual drive containing the Tor Browser application.
Instead, sites have complex .onion addresses, making them difficult to find without the exact URL. If you’re researching how to access the deep web, you’ll definitely come across Tor. And that’s no coincidence—it’s the most popular and trusted browser for exploring this hidden part of the internet.

All users who create a new Webshare account automatically receive 10 free (shared datacenter) proxies + 1GB/month bandwidth to use for as long as they want, no credit card required. The user who signs up will get a free basic plan, and also have a 25% discount when upgrading. For a limited time, new users who purchase any plan can claim 25% off their first order. The user will have the discount automatically applied after they click on it and check out. Copy your desired onion URL and paste it into the address bar at the top of the screen to begin searching on the dark web. Alternatively, if the website has turned the onion URL into a link, you can click on that in the Tor browser, and it will automatically open the dark website.
Open the downloaded file on your device to begin the installation process. The process is similar to installing any other software – follow the on-screen instructions and wait for the installation to complete. Once complete, you can add Tor to your shortcuts menu for easy access. The Onion Router (Tor) was developed in the 1990s by researchers and computer scientists at the United States Naval Research Laboratory. It derives its name from the encryption system, which is structured like the layers of an onion. To put it less technically, the entry node knows who you are but not where you’re going.
You should never use your personal information on the dark web anywhere else in your life. In fact, create new throwaway accounts and documents if possible. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Avoid using payment methods that can easily expose your identity. Today, many organizations exist that are created only to handle these reports anonymously and effectively.