Tor doesn’t support plugins because they introduce security risks. Malicious actors often target browser plugins to steal website credentials or install malware on unsuspecting devices, so Tor sidesteps these risks altogether. However, the most secure way to use Tor is via .onion sites, which are built exclusively for the Tor network. It’s extremely rare and only useful in very specific cases, like if your VPN is only accessible through Tor. With this setup, your ISP sees Tor usage, and your VPN provider sees the final traffic after it leaves Tor.
Safety First: Browsing Tips
Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal. The use of the dark web raises suspicion as it shows there is something you want to do privately.
Tor Browser User Manual

However, while Tor is great, safe, and whatever you think, it’s not as great as another component – a VPN. We must explain that Tor is safe on paper but practice has shown that this browser can fail you. Install Avast SecureLine VPN for iOS to protect your privacy and keep your data from falling into the wrong hands.
VPN over Tor requires you to place trust in your ISP but not your VPN and is best if you want to avoid bad Tor exit nodes. Some consider VPN over Tor more secure because it maintains anonymity throughout the entire process (assuming you pay for your VPN anonymously). Although the official Tor Project advises against VPN over Tor, both methods are superior to not using a VPN at all. You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions.
Many users, however, are simply everyday people who value privacy and choose to browse anonymously as a matter of principle. Dark web sites are hidden by non-indexing, making them completely anonymous. You’ll need a purpose-built browser that uses The Onion Router (TOR) to access dark web content.
How To Stay Safe While Using Tor Browser

On the other hand, the dark web hosts marketplaces and forums where illegal goods and services—such as drugs, weapons, and stolen data—are traded, making it a hotspot for criminal activity. Despite its negative reputation, not all activity on the dark web is malicious; some users rely on it as a tool for freedom of expression or to circumvent restrictions. The Dark Web is also known for hosting illegal and explicit content, including child exploitation material, snuff videos, and other highly disturbing or illegal material. These sites are often closely monitored by law enforcement agencies and are illegal to access or participate in. Like the regular surface web, the dark web offers its own social media sites and web forums. These platforms are often encrypted and anonymous to protect users’ identities.
Forums and websites on the dark web are not moderated, so you can never be sure they are free from malware. Therefore, you should avoid downloading files from the dark web, as seemingly innocent files may contain malicious software. While Tor lets you reach .onion sites, many require invitations, passwords, or verification. However, with the right security measures and cautious browsing, you can minimize these dangers.
Step 2: Install Hyphanet
Tor Browser has since become a popular tool of journalists, activists, and others that may be subject to being monitored online. This is why I strongly advise anyone visiting the dark web to exercise the greatest of caution during their dark online travels. Check out my article for more information about the dark web and how to access it while staying safe.
However, not all the forums and social media sites are legal on the dark web and often include shocking conversations and pin boards by anonymous users. Using Tor and the Tor Browser is considered relatively safe if you use the default security settings, but keep in mind that Tor does not provide end-to-end encryption. Likewise, it will not protect you from common digital threats like malware or phishing attacks. When using Tor, practice good security hygiene by avoiding suspicious links and using reliable antivirus software.
Dark Search
In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. In 2002 the dark web began to grow significantly when researchers backed by the U.S. Journalists in overly restrictive countries also appreciate the anonymity of the dark web. The users of the dark web are typically aiming to block governments from snooping on them.
We understand that because of the reputation looming over the dark web as being so dangerous, mysterious, and whatnot. Some sites are safe to use, especially those where you don’t need to provide sensitive information to use. ExpressVPN is slightly expensive but a trustworthy provider for risk-free dark web browsing. You’ll also enjoy its Smart DNS support, 24/7 live chat service, the Keys password manager, and a lot more. Feel free to grab its 49% discount thanks to 3 free months for the annual plan.
Why Would An Organization Access The Dark Web?
And though some dark web marketplaces offer user reviews, not all do. Lack of regulation by authorities or other users makes it easy for cybercriminals to carry out scams. It’s possible to buy and sell illegal drugs, malware, and prohibited content in darknet marketplaces. Some dark web commerce sites have dangerous chemicals and weapons for sale. As always, protect yourself from online threats with mobile Android security or iOS security software.
Despite this, tracing a specific user’s activity on the Tor network is highly difficult and rarely achievable. It’s important to note that even though your traffic is anonymized and routed, authorities can still subpoena servers and trace it. Tor, short for The Onion Router, is a privacy-focused network that allows you to browse the Internet anonymously. It works by routing your encrypted traffic through multiple volunteer-operated servers, known as onion routers. Tor is by far the most widely used dark web network and is the biggest network in terms of content and activities.
Components Of DOT Security’s Services
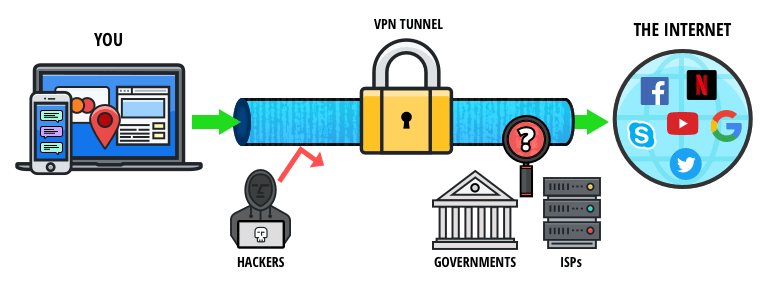
The Tor network combined with a VPN is one of the safest ways to get on the dark web. Many internet service providers (ISPs) and governments are suspicious of Tor use, but a VPN will hide your internet activity and help prevent anyone from knowing that you’re using Tor. VPNs are often recommended as protection in such cases, but Whited disagrees. The term “onion routing” reflects how layers of encryption are applied—similar to peeling layers from an onion. With each hop through the network, a layer of encryption is removed, concealing the user’s original location and identity.
- Access to “.onion” domains and anonymous surfing made possible by specialised software like the Tor Browser allows entry only.
- So, you risk being flagged or investigated for visiting certain sites, even without criminal intent.
- If you are in a position to report the incident safely, you should report it to the authorities immediately.
- Its main appeal is that it offers more privacy and supports legacy Firefox add-ons.
- It is designed to be used without leaving a trace on your computer.
- In addition, the content on the pages don’t need any special or custom configuration to access.
- This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs.
- Don’t log into any real accounts, reuse usernames, or enter any personal details.
- Often, these ethical hackers use their computer savvy to help governments agencies and big corporations hunt down vulnerabilities and in turn, create patches defenses for those system weaknesses.
- This includes avoiding logging into any personal accounts (social media, email, banking, etc.) while using Tor Browser.
- Law enforcement agencies worldwide monitor the dark web, and accessing these illicit markets, even out of curiosity, can draw unwanted attention and legal scrutiny.
Websites and data on the dark web do typically require a special tool to access. Prior to Keeper, Darren served as an advisor to JiWire, now called NinthDecimal. NinthDecimal is the leading media and technology service provider for the WiFi industry. He was formerly the Chief Financial Officer and a principal shareholder of Apollo Solutions, Inc., which was acquired by CNET Networks. Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims.