You can be sure that both Arkham’s intelligence analysts and law enforcement will be doing precisely that. If you get an alert that your personal data, like an email address, password, phone number, or social security number, was found on the dark web, you don’t need to panic, but you should act fast. Accessing the dark web is easy; you just need the Tor Browser, which connects you to the Tor network where .onion websites live. For journalists and activists, the dark web serves as a vital tool for safely exchanging sensitive information. Platforms like SecureDrop and GlobaLeaks give whistleblowers a way to share documents without revealing their identity.
Bitcoin: Perils Of An Unregulated Global P2P Currency
The price of Bitcoin has shot up astronomically since the company’s heyday; at no point in 2016 did BTC cross the $1,000 price point. So-called “ancient” Bitcoin whales pop up in the space periodically, but an extant darknet vendor is still quite rare. Nucleus’ assets have appreciated in value astronomically, but it will be very difficult to convert this BTC into fiat currency.
Share This Article
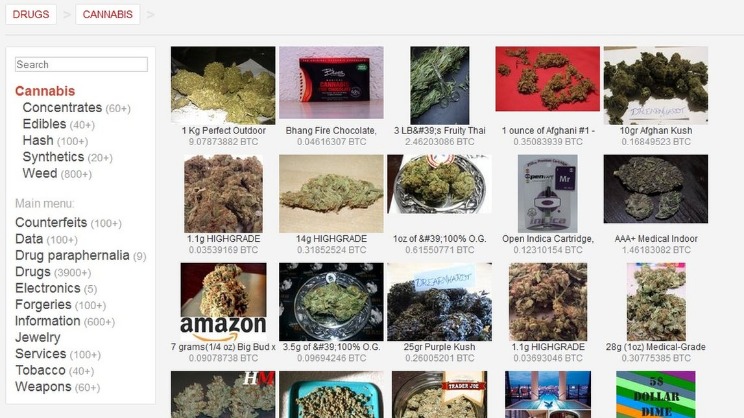
Many expect Q to follow a similar pattern, with rallies potentially intensifying into November. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures. But platforms such as Silk Road helped Bitcoin gain notoriety, as it served as a means of payment there.
Shuttered Dark Web Marketplaces
Bitcoin’s adoption depended on markets like Silk Road to pioneer, and what was special about Silk Road is that it was an almost completely free (as in freedom) market. Free markets are excellent for adoption because they don’t require bureaucracy, permits, regulations or any other form of permission to run. They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails.
Emergence And Structure Of Decentralised Trade Networks Around Dark Web Marketplaces
Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers. Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. To find out which darknet markets are currently popular, and the .onion URL required to visit each one, see Darknetlive.com or dark.fail. Dark.fail lists numerous darknet sites, including forums; scroll down the page until you see the names of darknet markets and look for the green light beside the URL to denote that it’s currently online. According to Chainalysis, several factors likely contributed to this dramatic growth.
This information can be useful for identifying opportunities for collaboration or for comparing the research funding landscape in different countries. Research on the Darknet will likely interest many countries and organizations due to the potential implications for cybercrime, national security, and internet governance. The cryptocurrency market posted solid gains over the past 24 hours, pushing total market capitalization to $3.86 trillion, up 2.34%. In successful cases, law enforcement can combine this intelligence with other investigative techniques to seize the online infrastructure and residual virtual currency, like in the case of the Silk Road seizure. In the wake of recent headlines announcing actions against Hydra Marketplace by the U.S. and German governments, darknet markets have made an ironic entrance into the spotlight. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
Hidden Cyber Risks Of Generative Artificial Intelligence
There’s no way to delete personal data once it is circulating on the dark web. Your best option is to take steps to make sure your information is useless to criminals. For example, it’s a good idea to change your passwords, contact your financial institutions, freeze credit, and set up two-factor authentication.
Swiss Bank Sygnum Launches BTC Alpha Fund, To Grow Bitcoin 8–10% Annually
A while back I made another blog post on PGP keys which helps explain what PGP is and how it works. The intersection of cryptocurrency and the darknet markets is a complex ecosystem. Many users wonder what bitcoins are accepted by darknet markets and how these currencies are utilized.
It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. Others are looking for stolen data, hacking services, or even banned books and political content. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims.
- This research has used local Bitcoin trade volume as a proxy for adopting cryptocurrencies in the shadow economy and has found evidence of currency substitution in some cases.
- If you’re using Localcryptos, press the yellow button marked ‘Transfer’ and then sit back and wait.
- Despite its name, the marketplace operates primarily in English and serves a global audience.
- Cybersecurity companies, researchers, and law enforcement agencies (including FBI) monitor the dark web.
- Additionally, many markets now integrate PGP encryption for communication, further safeguarding sensitive information.
For each entity, we keep track of the cumulative values of the six features for each transaction performed by the entity over time. To be classified as a seller, an entity must simultaneously satisfy the six feature threshold criteria, as follows. Indeed, one of the most recent darknet market busts was the Nemesis online market. The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) specifically cited the market’s role in the fentanyl trade as a reason for the bust. On-chain data from BitInfoCharts shows that the daily number of monero transactions has halved from this time last year. “After major exchanges delisted XMR, we observed a significant increase in bitcoin inflows,” Jardine said in an interview with CoinDesk.
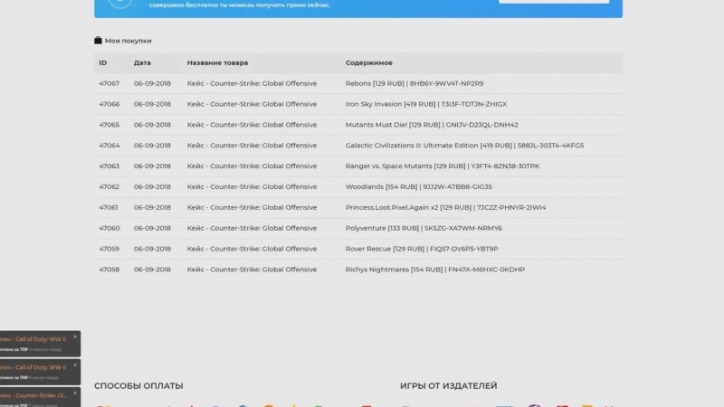

In this case, the features of bitcoins – anonymity, ease of cross-border transactions and finality of settlement – were a perfect vehicle for criminals to conduct their illegal activities on the site. In this context, the report says that the graph indicates the dark net users are attempting to conceal their Bitcoin flow within the dark web spectrum. By C Dion-Schwarz 2024 Cited by 54 might increase their use of such digital cryptocurrencies as Bitcoin to terrorist use of darknet markets for acquiring weapons is a troubling. Larry Harmon, 38, admitted that he operated the Bitcoin mixer called Harmon admitted that Helix partnered with several darknet markets. Results are gathered from Ahmia and Onion City Darkweb’s search engines, and anonymity is also discussed.

It’s Back To Bitcoin For Darknet Markets After Monero’s Binance Delisting: Chainalysis
Some markets accept Bitcoin Cash (BCH) and various privacy coins like Monero, but these are not classified as Bitcoin. Tor establishes a secure network circuit for each browser session, which connects Tor nodes deployed around the world at random. These nodes encrypt your browser traffic in layers at each node hop on its way to/from the source (your browser) and the destination (a hosted hidden service). Private Internet Access has 10+ years of experience leading the VPN industry.