
In fact, previous studies on DWM transaction networks have revealed crucial aspects of the ecosystem13,14,15. However, they have so far mainly focused on DWM users, without distinguishing between buyers and sellers, and neglecting the different weight that more active users may have in the system. The reason is that the operational structure of DWMs inherently hides the seller–buyer link, as all transactions are made through the marketplace. Buyers send money to the marketplace, which in turn sends the money to the seller. Thus, further analyses in this direction have been hindered by the lack of heuristics able to identify these two key classes of actors in transaction networks and their roles in the structure and dynamics of the ecosystem. Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum.
However, owing to the difficulty of identifying relevant transactions, most studies rely on user surveys17,18 and data scraped from DWM websites19,20,21,22,23,24. In particular, these studies are based on user reviews which carry many inaccuracies, for instance, with respect to the time and value of the transaction19, that further compound error in other measures. Moreover, data scraped from the DWMs cannot assess the U2U transactions which account for the largest fraction of the total trading volume of the ecosystem13. The darknet is used for anonymous communication, accessing censored information, and protecting privacy. Journalists and activists use it to communicate securely in oppressive regimes. You can access it for legitimate purposes like whistleblowing and freedom of expression.
Q: What Advantages Does Cryptocurrency Offer On The Dark Web?
In practice, this means potential buyers and sellers may undergo background checks within forum communities before receiving an invite. This layered approach, combining encryption, strict moderation, and personal referrals, aims to preserve the secrecy and continuity of the marketplace. Bitcoin remains the most widely recognized, though it has become easier to trace through blockchain analytics. As a result, privacy-focused coins like Monero and Litecoin have gained traction among those seeking tighter anonymity. Some marketplaces also explore emerging alternatives, offering greater obfuscation techniques to bypass law enforcement surveillance. About TRM LabsThis report was written by TRM Labs, the blockchain intelligence company.

However, compared to sellers, the drop is notably smaller, and the number of buyers rapidly recovers to previous values. Moreover, the number of multibuyers increases, which suggests a fast response from buyers to external shocks by trying to diversify their sources. Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks. In repressive regimes, darknets play a vital role in enabling free speech and access to uncensored information. Tools like Tor are used to bypass government-imposed firewalls and surveillance, ensuring open communication. The significance here is the preservation of civil liberties and the right to information.
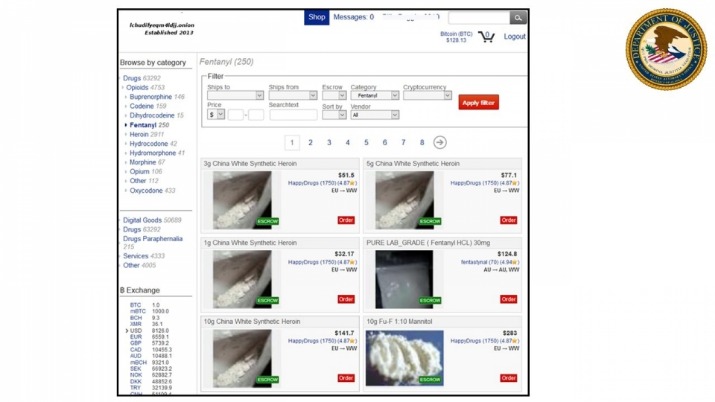
The Emergence Of Marketplaces On The Darknet
Therefore, key actors in the ecosystem of DWMs may play important roles in broader criminal networks. The finding that multisellers and, in specific cases, multibuyers play a central role in connecting the ecosystem, thus contributing to its resilience, may illuminate how to better target future law enforcement operations. In general, by understanding the operation of key players within the DWM ecosystem, our work highlights how appropriate strategies can be designed to counteract the online trade of illicit goods more effectively.
Core Security Features:
The dark web, a hidden part of the internet accessible only through special software, is notorious for its illicit activities and underground marketplaces. Cryptocurrencies like Bitcoin and Monero have become the preferred choice of currency on these platforms due to their decentralized nature and ability to provide discreet transactions. Dark markets are online platforms on the darknet where illegal goods and services are traded.
TorZon Market
Additionally, we analyse the U2U network of transactions, i.e., the transactions between pairs of market first-neighbors where the source and destination nodes are market users without the market as an intermediate. In the U2U network, an edge connects nodes that are not necessarily users of the same market. Previous studies have shown that, although the number of users and transactions is larger in markets, the trading volume in the U2U network is larger than that of markets13. We use data of DWM transactions on the Bitcoin blockchain pre-processed by Chainalysis Inc.
Intellectual Property Crime
Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance. Using a dark web search engine is a great step towards enjoying a more secure experience while shopping on the platform. Not all marketplaces you want to visit can be accessed through regular search engines.

However, nearly as soon as Hydra shut down, OMG began seeing high inflows for the first time, more than half of which came from Hydra counterparties. The most common and convenient way to access the dark web is to download & install the Tor browser. It automatically routes all the traffic through the Tor Network, allowing you to stay anonymous. One of the main concerns regarding the future of cryptocurrency on the dark web is the potential for increased regulation.
Common Categories Of Illicit Content
- Tor (The Onion Router) remains the most popular, routing data through multiple encrypted layers to hide users’ real IP addresses.
- Fundraising campaigns for ISIS families held in internment camps in northeastern Syria has been a significant driver of cryptocurrency usage among ISIS and its supporters.
- Other than the Silk Road 2.0, similar marketplaces also emerged, but they all went down sooner or later.
- Crypto ATMs and other cash-to-crypto services are not illegal; however, they can be an appealing payment method for cybercriminals and other illicit actors.
- The vendors aren’t required to register or apply for a vendor account while using this platform.
Despite promising investors healthy returns, the criminals used investor funds to buy real estate, jewelry, cars, boats, and luxury clothing. One challenge for such on-chain surveillance is that criminals frequently cash out using brokers who exchange physical banknotes for privacy coins deposited to their receiving address. The cash is then smuggled across borders while the cryptocurrency is traded on exchanges. Chain-hopping refers to the practice of moving cryptocurrency from one blockchain to another. While chain-hopping is not inherently illicit, it can be used by money launderers to obfuscate the transaction trail.
Torrez Market
Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet. Our team searched the dark web and put together a list of the most active dark web marketplaces in order to assist you in monitoring illegal trade of products, cybercrime activity, and dark web trends in the dark web space. Additionally, The Financial Action Task Force (FATF) enforces Anti-Money Laundering (AML) and Know Your Customer (KYC) measures to enhance transparency. The Travel Rule mandates transaction disclosures, aiding law enforcement in tracking illicit funds. Regulatory bodies leverage blockchain analytics to combat money laundering and fraud, strengthening global enforcement efforts.

Ponzi And Pyramid Schemes In The Digital Era
Understanding the driving forces behind their growth—alongside the mechanics of how they function—is crucial for both cybersecurity professionals and policymakers tasked with mitigating emerging threats. Cryptocurrency mining has been abused for laundering funds by ransomware groups, such as APT43, and other illicit actors. The coins minted on mining equipment acquired with illicit funds have no apparent ties to criminal activity, allowing criminals to cash out without leaving a traceable path on the blockchain.
Treasury Payments
The outputs from the mining transactions were then laundered through a Bitcoin ATM business controlled by the vendor, which provided a front for the illicit activity. It is important to note that many DeFi platforms are actively implementing measures to enhance security, compliance and transparency. Regulatory authorities are also working on frameworks to address money laundering risks in the context of DeFi.
This article sets out to illustrate how the leading Dark Web marketplaces are structured in the years 2024–2025. By delving into their core offerings—ranging from illegal narcotics to sophisticated hacking tools—we can gain a clearer perspective on the criminal ecosystem that fuels a substantial portion of online illicit trade. In 2021, SUEX, a Russian-language OTC broker, was sanctioned by OFAC for facilitating financial transactions for ransomware actors. Cryptocurrency-based gambling platforms make it difficult to trace funds through the service. This means that casinos must perform KYC and source of wealth checks on customers seeking to deposit large amounts. Later, should a suspected criminal claim gambling winnings as the source of their funds, the online casino in question can be subpoenaed by local law enforcement to release records relating to that user.
There have been several high-profile cases of proven or alleged bribery involving crypto. In 2021, FTX founder Sam Bankman-Fried allegedly gave a USD 40 million cryptocurrency bribe to Chinese officials in exchange for unfreezing company accounts containing over USD 1 billion worth of cryptocurrency. Other instances of people accused of using cryptocurrency to pay hitmen have been reported elsewhere. In 2022, a Mississippi resident received a 10-year prison sentence for attempting to have her husband killed for a USD 10,000 fee in bitcoin. It’s impossible to tell with certainty whether the activity is actually malicious, let alone illegal, without knowing more specifics, said Chainalysis Director of Research Kim Grauer. Still, the data suggests widespread “potential shenanigans” (as one observer called it) that warrants attention and study.
The platform also cares about its users and uses PGP encryption and two-factor authentication to secure their data and communication. To prevent users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers. Moreover, this shop provides detailed statistics about each user profile on the platform, giving users a better idea of the vendors for the buyers and vice versa. This marketplace accepts payments via Monero but also supports the Escrow system. Despite consistent results, this study has limitations that may be addressed in future work.



