Despite what the name implies, it isn’t illegal to access the dark web. It provides individuals with privacy and anonymity that traditional websites don’t offer. For instance, people can go on the dark web and post their thoughts about political activity without being reprimanded by government officials and other groups. If you have something to say and people are into it, you can be found, and that is a remarkable quality of the modern platforms, regardless of all their other ills.
Stay One Step Ahead – Protect Your Data From The Dark Web
To reach Geekflare.com, you can either type its URL in your standard web browser or search for Geekflare in your favorite search engine. And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics. Well, now it’s time to fire up Tails and do a little bit of tinkering. Chill, because nobody will ever find a record of you ever fiddling around the darknet.

How To Access The Dark Web Safely And Securely

This includes accessing restricted channels and automating intelligence gathering to anticipate attacks targeting your organization, employees, and customers. For instance, if a threat actor is in possession of stolen data from a large healthcare provider, security personnel acting on behalf of the company are likely to conduct a large portion of that investigation throughout the Dark Web. Threat intelligence gathered from the Deep and Dark Web is likely to help future threat hunting teams when analyzing telemetry from beyond their own networks, such as the Deep and Dark Web.
The use of mixers and tumblers to obfuscate transaction trails is also on the rise. Privacy coins like Zcash and emerging protocols leveraging zero-knowledge proofs are gaining attention for their ability to further mask transactions. “This shift complicates law enforcement’s ability to track illicit financial flows, pushing agencies to invest in new blockchain forensic tools and cross-chain analytics,” Kurrie says. AI has the ability to accelerate the scale and sophistication of cyber attacks and it’s starting to be incorporated into tools and services on the dark web.
Is The Dark Web Used For Illegal Purposes?
The interesting point though on this, that I see, is that there is a moment where that doesn’t end up being the case, meaning there’s a moment towards the early days of the web where people did look back to and say, “All right. That’s where I think the folks on AfroNet, who had built that bulletin board system of Black users, came into play, all the people that were playing in that world of the internet of ‘88 and ‘89 and the ‘90s. Another part of my fascination with it is that a lot of people don’t know that Under Armour is a very conservative company. Before they focused on athletes, Under Armour heavily catered to law enforcement. I’m fascinated by it being a staple in the hood, but then a staple among law enforcement too.
What Is The Difference Between The Deep Web And The Black Internet?
- This is because Black Web communities are more connected than typical websites and when a new website or platform is developed, lots of people hear about it.
- This means that the JavaScript will be disabled by default on every website and some symbols and images will not be displayed.
- Abuse and persecution victims, whistleblowers, and political dissidents have been frequent users of these hidden sites.
- To access a dark web resource, you will need to know its web address to the letter.
- I talked to William, and out the gate, I asked the question, and he said, “I don’t know.
The dark web — aka, the deep web — is the second layer of the internet, which is not indexed by search engines. Websites and pages in the deep web might include password-protected content, private forums, and personalized resources. However, anonymity and privacy of the dark web also contribute to various crimes, such as black markets for illegal drugs and materials, human trafficking, the trade of stolen sensitive data, and access to extreme content. As hoped, the Tor anonymous network grew in popularity among computer enthusiasts, privacy advocates, journalists, dissidents under repressive governments, and others desirous of strict secrecy.
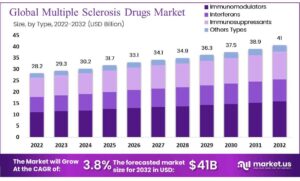
Dark web monitoring can supplement other tools used to gather preemptive threat intelligence, such as the Mitre ATT&CK framework. Ironically, the Tor network surfaced in 2006 from a legal project jointly funded by the U.S. It was largely the introduction of Bitcoin in 2009 that transformed the dark web into a sanctuary for criminals. Bitcoin also contributed to the emergence in 2011 of the Silk Road, a black market for buying and selling illegal drugs. The dark web’s anonymity accommodates illegal activity and contributes to its reputation as being a haven for criminals. This anonymity, coupled with access difficulties and a high barrier to entry, facilitates all manner of illicit activities such as drug and human trafficking, weapons deals, and money laundering.
How To Access The Dark Web
Therefore, you should understand the legal risks of accessing the dark web before you venture into this murky world. However, we strongly advise against using dark web marketplaces due to legal risks and the high likelihood of being scammed. Freenet is a decentralized, peer-to-peer platform designed for the secure and anonymous sharing of information over the Internet.
In other words, the deep web covers everything under the surface that’s still accessible with the right software, including the dark web. Tor is the most popular instance of a darknet,19 and it is often mistakenly thought to be the only online tool that facilitates access to darknets. With the rise and fall of the Silk Road—and then its rise again and fall again—the last couple of years have cast new light on the Dark Web. But when a news organization as reputable as 60 Minutes describes the Dark Web as “a vast, secret, cyber underworld” that accounts for “90 percent of the Internet,” it’s time for a refresher.
Ways Small To Midsize Businesses Can Stay Safe In The Cloud
On the flip side, you’re saying the police are getting more and more dehumanized for the communities they serve because of technology. I used to have a chapter of the book in an earlier version that was titled “Remember When the Internet Was Black? The deep web and the dark web have a lot of uses, but they also aren’t without their risks.
There are different levels of security in the browser that are worth considering. To review security settings, click on the onion logo in the top left and select “Security Settings”, which will bring up a slider offering a choice of the default of standard, or safer and safest. In “safer” mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won’t run automatically, you’ll have to click to play. Slide up to the “safest” level, and as well as those settings, JavaScript is disabled on all sites.
WeTheNorth is a Canadian market established in 2021 that also serves international users. It offers counterfeit documents, financial fraud tools, hacking and malware services. It has an active forum and community along with an extensive user vetting process. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information.
Fraud and scams run rampant on the dark web, including offers too good to be true and fake services requiring upfront payment. Hackers sell access to email accounts, social media profiles, or other information that can be used for identity theft. Surface web search engines can’t access the darknet, but specialized dark web search engines can help you find what you’re looking for. DuckDuckGo is a popular privacy-focused search engine that doesn’t track you across the web.
Also known as The Onion Router, TOR enables users to browse the Internet, including the Dark Web, anonymously. It bounces traffic through several servers before delivering it to its destination, making it harder to track a user’s activity or location. The dark web often carries a negative connotation, largely due to its association with illegal activities. However, it also offers significant advantages, especially in terms of privacy and security. For individuals living under oppressive regimes or anyone needing to communicate away from the watchful eyes of surveillance, the dark web is a valuable tool.
Generative AI Is Making Attacks Easier For Those Less Schooled In Technology
However, today’s most popular search engines — including Google, Bing, and DuckDuckGo — only index a portion of the internet. Therefore, you should stay cautious and avoid clicking when accessing the dark web. Doing so will protect you from accidentally accessing illicit content or becoming a victim of malware. Additionally, much of the materials on the dark web are illegal, and unknowingly downloading such content can implicate you in criminal activities punishable by laws. If your device is infected with malware, read our guide to remove malware from your computer.
Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. In this guide, we’ll show you what you need to know about how to access the dark web and how to keep yourself safe while you use it.