You can tell you’re on the dark web if you’re accessing websites with .onion addresses on the Tor Browser or a similar anonymity network. These sites aren’t accessible via standard web browsers or search engines. Unlike traditional search engines, it doesn’t track or store personal information, ensuring your searches stay private. It’s a popular choice for users worried about online surveillance and data collection. If you exercise due caution and use a combination of the Tor browser and common sense in which sites you access on the dark web, yes, the dark web is safe to use.
Update Your Tor Browser
No one really knows the size of the dark web, but most estimates put it at around 5% of the total internet. Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable.
Discover Content
For this reason, you must watch out and avoid opening anything that looks suspicious to you. You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet. Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal.
Disable Java And ActiveX In Your Network Settings
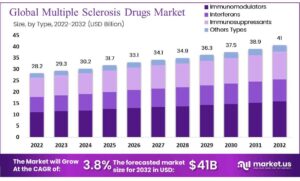
Google doesn’t index these sites, but other search engines do, including DuckDuckGo, and there are lists — including one run by Muffett — so you can find what you’re looking for. (a) The number of sellers for each category and multisellers per quarter. (b) The number of buyers for each category and multibuyers per quarter.
Bitcoin Services
It is designed to be used without leaving a trace on your computer. It also comes with several secure pre-installed software programs, including the Tor Browser. This guide reviews tools such as Tor, I2P, Whonix, and more for accessing the hidden web securely. Avast BreachGuard monitors the dark web for data breaches around the clock. If a breach is detected, BreachGuard will notify you right away and help you take the steps you need to secure your data immediately. Track and analyze darknet activities using our advanced cyber threat intelligence platform to stay ahead of emerging threats.
Buyers And Sellers

STYX MarketSTYX Market, launched in 2023, is all about financial crime. It offers access to hacked bank accounts, credit card data, and cryptocurrency laundering tools. Transactions can be made using Bitcoin or Monero, and the platform keeps users in the loop through an official Telegram channel.
Supporting Illegal Activities Unknowingly
- Using a reliable VPN like ExpressVPN with dark web search engines is essential for protecting your privacy.
- ZeroBin encrypts any text pasted into it, and its own servers don’t even know what you pasted.
- This layer contains all the online content that isn’t crawled or indexed by search engines.
- ProtonMail’s end-to-end encryption makes it one of the best onion sites for easy-to-use, secure, anonymous email.
- You only need to upload your PGP key or let the platform create one.
I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination.
In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web. In 2002 the dark web began to grow significantly when researchers backed by the U.S. The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe. Journalists in overly restrictive countries also appreciate the anonymity of the dark web.

For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities.
Types Of Dark Web Sites (and What Really Goes On There)
Plus, it features a built-in VPN to encrypt your connection, hiding your IP address and online activity, for more anonymous and private browsing. Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered. And though some dark web marketplaces offer user reviews, not all do. Lack of regulation by authorities or other users makes it easy for cybercriminals to carry out scams.
We showed that a small fraction of traders is responsible for a large fraction of the trading volume, and by analysing the networks of buyers and sellers, we found different resilience regimes. Shocks tend to induce serious structural changes in the multiseller network, but impact the multibuyer network much less severely. Interestingly, the S2S network shows an intermediate level of resilience, which suggests that the S2S network might play the role of a supply chain network on the dark web. Furthermore, after a shock, the activity of buyers is resumed almost immediately, while the activity of sellers recovers more slowly. These different regimes suggest that the ecosystem’s resilience is mainly supported by the high demand of buyers rather than the response of the sellers.
Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
Is It Illegal To Visit Onion Sites?
The EDTF encompasses a standalone Cyber Division as part of an effort to stay abreast of emerging criminal threats and in keeping with current and future investigative priorities. The EDTF’s mission is to disrupt, dismantle or render ineffective organizations involved in the laundering of proceeds of narcotics trafficking and other financial crimes. Since its inception in 1992, the task force has been responsible for the seizure of approximately $600 million and more than 2100 arrests. You can use dark web monitoring services or free tools like haveibeenpwned.com to check if your email, passwords, or other personal data have appeared in known dark web data breaches or dumps. Several secure email providers, such as Riseup and Mailbox.org, provide onion sites for users who want to add an extra layer of privacy and anonymity to email communications.
Dark Web Monitoring And Identity Theft Protection At Your Fingertips
By following these precautions, you can explore the dark web with a greater degree of safety and security. Ahmia promotes transparency by being open-source and allowing contributions. Its operations focus on respecting user privacy and maintaining anonymity through the use of the Tor network. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. It has a bidding feature, with new batches of stolen data being frequently added.