As retailers accept mobile payments and other forms of online payment, payment processors have become increasingly common. The value of a hacked account will fluctuate because these entities vary in cybersecurity capabilities and insurance. Here’s another snapshot of a vendor profile to further illustrate how this marketplace is thriving. Notice how it normalizes fake data buying by including buyer ratings and comments. When you access a website, email account, network server, or another password-protected item, you can save the password in your keychain so you do not have to remember or enter the password each time.
Hacked Online Services & Entertainment Accounts
By setting up alerts, businesses can receive notifications whenever their PII or credit card information appears in suspicious contexts. This proactive monitoring enables businesses to track and investigate potential threats in real-time, helping to prevent fraud before it can impact their operations. The use of such platforms is crucial for maintaining the integrity and security of customer data, and it provides an additional layer of defense against cybercriminal activities. Stolen identity data is exploited for a variety of malicious purposes. Identity theft is a primary use, where criminals open accounts, apply for loans, or make purchases in your name.
- These systems can often identify when stolen card data is being tested before major fraud attempts begin.
- PayPal accounts sell for $2 to $10 per account, with accounts holding more money costing even more.
- Bitcoin () is system tool that will act as a personal bank for storing and investing digital currency on your computer.
- Considering this backdrop, it is evident that b1ack’s primary goal has consistently been to profit from the sale or use of these stolen credit card details.
- This market is one of the easiest to use and is very simple for inexperienced dark-net users.
Cybersecurity Awareness Explained: Importance & Best Tips 2025
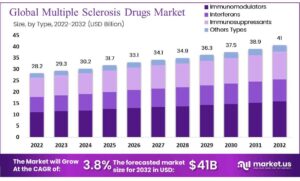
Credit card fraud in itself is an enormous 32 billion dollars industry, and is only expected to grow in size, upwards of 38 billion dollars by 2027, according to a report by Statista. It is essential to understand that participating in credit card transactions on the Dark Web is illegal and unethical. Engaging in illegal activities can lead to severe legal repercussions, including fines and imprisonment. Moreover, the financial repercussions for victims of credit card fraud can be devastating. It is important to highlight that participating in credit card transactions on the Dark Web is illegal and unethical.
- “White House Market was unusual in that it was pretty much a walletless market, although it did not advertise itself as such,” says Ormsby.
- In our scenario we are going to check out the Black Market Reloaded and look for the current price of some credit cards and tools.
- A fair number of vendors include access to a SOCKS5 internet proxy that can be used by the buyer to match their computer’s IP address location with that of the cardholder in order to avoid being blacklisted.
- It helps us stay more vigilant, better protect ourselves, and make informed decisions online.
Every virus, worm, bot, and other piece of malware is created by a specific company. The leaders of criminal organizations coordinate with programmers to develop malware, hackers to infiltrate networks, or other con artists to develop spam and phishing attacks. Windows users and online users who have been conned when looking up specific information, conducting banking transactions, or using networking are frequently the victims. The dark web offers a marketplace for buying and selling private data, but it’s also a location where users may hide their identities and their transactions. It is difficult to put an end to fraudulent operations or repair the harm done to customers because of a lack of control and common security measures. Cyble Research Team has correlated the leaked credit cards information details (and the BINs) with the respective banks, their location (country) as well their types, etc.
More From Moneycom:
Despite the pseudonymous nature of cryptocurrencies, law enforcement agencies and cybersecurity experts have developed sophisticated techniques to trace these transactions. Now that we understand why individuals are enticed to buy credit cards on the Dark Web, let us explore the risks and challenges involved in these transactions and how to navigate this treacherous landscape. With stolen payment cards, a cybercriminal can immediately make purchases under your name, or even drain your bank account.
Trend Micro Cyber Risk Report

Zero-days are mostly thought to be used for corporate espionage, or for specific targets whose only entry is through a zero-day. Some companies have set up their own bug bounty program to avoid selling their zero-day vulnerability in black markets. Many simply install free software for enabling anonymous communication and direct internet traffic through a free, worldwide, volunteer network consisting of more than seven thousand relays. The user’s location and the usage are hidden from anyone conducting network surveillance or traffic analysis. Most of these free software options make it more difficult for Internet activity to be traced back to the user, including website visits, online posts, instant messages, and other communication forms.
FBI Can Neither Confirm Nor Deny Investigations Into Darknet Markets That It Confirmed Are Ongoing
This often includes a “checker service,” a compromised merchant account they use to run dinky charges through to see if the card is still valid, Krebs says. If someone agrees to use the shop’s checker service instead of a third party, the shop will give a guarantee that at least a portion of the cards are usable for a certain period of time. On these hidden illegal websites the goods are usually sold at deep discounts on the black market, usually around 50% of retail and reshipped or sent to a secure drop (vacant house etc) a purchaser has setup for this purpose. If these transactions are being executed on your corporate network, that activity can expose your organization to legal and other risks. After your Dwolla transfer moves to MtGox, you can use the money to purchase Bitcoins on the open market for a small percentage-based fee.
Cyble Strato Cloud Security
Most of use just have the standard personal account, but Premier and Business accounts also exist, and are up for sale on the dark web. But those tiers don’t have much influence on dark web prices, which are largely governed by account balance. Wizardshop.cc was established in 2022, and offers a wide range of leaked CVVs, database dumps and even RDPs. In the past 6 months, the site has increased the volume of cards sold, placing itself as one of the top sites selling credit cards today.
If identity theft is your major concern, use the following tips to reduce the chance of unwelcome visitors. People generally buy these accounts due to content restrictions on their own accounts. The hacked accounts may be from country that has a bigger streaming site library than their own. This is kinda weird because people can use a VPN to unblock streaming sites.
Unless you live the rest of your life only paying with cash, you’ll never be totally impervious to payment fraud. A major survey on Aussies’ ethical concerns has revealed Gen Z’s shift away from artificial intelligence, as social media platforms hit record-low trust levels. That breach, caused by an attack that compromised POS (point-of-sale) devices, went undetected for nine months. The breach affected 860 convenience stores – 600 of those were also gas stations. Ben Luthi has worked in financial planning, banking and auto finance, and writes about all aspects of money.
Threat Actors’ Motives
This time, the leaked data contains card numbers, expiration dates, and three-digit security codes (CVVs). The expiration for most cards reviewed by BleepingComputer ranges from 2025 to 2029, but we also spotted a few expired entries from 2023. BidenCash shop was established in April 2022, following the seizure of other card shops and carding platforms by the Russian authorities. Since its inception, it has been attracting the attention of both old and new cybercriminal customers. The threat actor initially focused on giving away freebies but eventually began promoting their shop on various dark web forums on April 16, 2024, ahead of their major launch at the end of April.

Zelle, Big Banks Challenge Senators On Scam Reimbursements
International law enforcement agencies led by the FBI have seized a sprawling dark web marketplace popular with cybercriminals, where stolen passwords were sold for as little as $1 each, officials announced this month. In this post, we’ll cover how credit card fraud operates on the dark web, how criminals obtain and trade card data, and cover some essential prevention strategies. Criminals in these cases will attempt to secure the ransom payment after data has already been stolen and put up for sale on the dark web, according to Mr Foss. In 2019, cybercriminals sold more than 30 million credit card records on the dark web, linked to a data breach at a US gas station and convenience store chain. If you’ve ever wondered where your stolen credit card turns up, a cybersecurity firm is offering hard proof.