
The integration of advanced encryption technologies and decentralized systems ensures that transactions remain confidential, while user feedback mechanisms enhance trust among participants. The darknet has become a cornerstone for secure and efficient drug trade, offering users unparalleled privacy and reliability. By 2025, several platforms have emerged as leaders in this space, leveraging advanced encryption, decentralized systems, and user-friendly interfaces to ensure seamless transactions. User reviews and vendor ratings play a critical role in maintaining trust within these markets. Platforms like Empire Market 3.0 have implemented advanced feedback systems, allowing users to evaluate vendors based on product quality, delivery speed, and communication.
Best Dark Web Sites: Unseen Onion And Tor Links
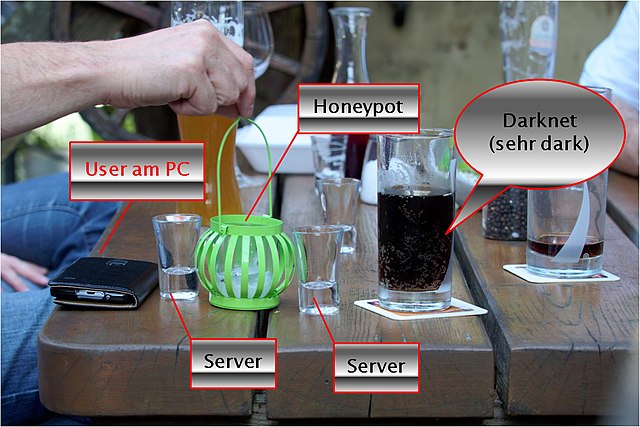
In 2025, darknet markets continue to provide a secure and efficient platform for the trade of pharmaceuticals and digital products. These platforms leverage advanced encryption technologies and decentralized systems to ensure user privacy and transaction security. The integration of cryptocurrencies like Bitcoin and Monero has further enhanced the reliability of these markets, offering users a seamless and anonymous payment method. The darknet is used for anonymous communication, accessing censored information, and protecting privacy. Journalists and activists use it to communicate securely in oppressive regimes. You can access it for legitimate purposes like whistleblowing and freedom of expression.

Malicious Software
Keeper has millions of consumer customers and the business solution protects thousands of organizations worldwide. All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web. Estimates place the size of the deep web at between 96% and 99% of the internet.
The New York Times
The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely. Always exercise extreme caution when using publicly posted onion URLs. If you can’t get a personal recommendation from someone you trust, verify the URL from multiple sources.
News, Media, And Other Information Organizations
One of the German officers charged with analyzing the contents of the CyberBunker servers told me that the volume of data was unwieldy, but its content fascinating. “I do not recall any case where this huge amount of criminal-infrastructure data was gathered,” he said. The technology behind this anonymous connection is known as “onion routing,” which utilizes a layered approach to obscure data and protect users’ locations on the network. Then there’s the less popular VPN over Tor, which is advised against by the official Tor Project. Only two VPN providers that we know of, AirVPN and BolehVPN, offer this service, although neither of these score highly for speeds. Internet traffic first passes through the Tor Network, and then through the VPN.

Frequently Asked Questions (FAQs) About Dark Web Marketplaces

Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats. Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents. The significance lies in the potential compromise of national security. Governments and businesses must invest in advanced threat intelligence, cyber defense, and counter-espionage measures. Dark markets, as well as various other services within darknets, are hosted as ‘hidden services’.
- Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents.
- Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias.
- It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications.
- Due to the nature of the money crossing hands, users of Darknet markets should be extra wary while using the services available.
Dark Web Links: The Best Onion And Tor Sites In 2025
Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. Those who access the dark web do so via the Tor (The Onion Router) browser.
Once the buyer confirms satisfaction, the funds are released to the seller. Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user reviews, ratings, and customer support. These features help create a sense of ‘trust’ among users, even in the criminal ecosystem. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data.
Alphabay Market
Engstrom allegedly used a cryptocurrency-to-cash exchange called BitLiquid to convert his earnings to US dollars. He exchanged Monero for Paxos Standard, a type of tethered cryptocurrency pegged to the US dollar, and then used BitLiquid to exchange that for cash. The DEA agents on Engstrom’s trail, meanwhile, used toll records to determine when Engstrom visited BitLiquid on his phone and monitored the BitLiquid wallet for activity in those time frames. One transaction that lined up—an exchange of $37,000 in Paxos Standard for $36,900 in cash—automatically triggered a currency transaction report, or CTR, because it was over $10,000. That CTR allowed investigators to trace Engstrom’s deposits to his personal crypto wallets totaling $3 million—money that investigators believe come from dark web cocaine sales. The first such modern black market to demand public attention was Silk Road—a $1.2 billion operation at its peak.
- These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.
- Wasabi Wallet is a Bitcoin wallet that not only hides all your data in the Tor network but also allows you to “join” your transactions with others to increase your anonymity.
- The platform allows buyers to review the vendor’s products and services, so it’s easy for them to decide if the vendor is reputable or just scamming them.
- These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”.
- For safer browsing, it is highly recommended to also use a VPN and antivirus software.
Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year. Other than the Silk Road 2.0, similar marketplaces also emerged, but they all went down sooner or later. Tor2door Market is among the largest dark net shops you must visit in 2025 if you’ve decided to visit such sites.
It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely. While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored.

And while the dark web isn’t synonymous with illicit activities, it’s undeniably the breeding ground for the internet’s black markets, hacker forums, malware vendors, and other illegal activity. In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere. You should be aware that law enforcement agencies may be monitoring the dark web and that visiting certain websites or engaging in illegal activities can result in criminal charges. You can also check out this ultimate dark web safety guide to browse safely. As when visiting ordinary websites, stay alert to security risks on onion sites. Don’t click on suspicious links, be skeptical of what you read, and avoid dark web marketplaces if you don’t want to stumble on illegal activity or content.
For recommendations on choosing a VPN, look for expert reviews and articles. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. To get on the dark web, you need a browser built for the job, and the best in the business is Tor.
ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users. The market has built trust among users as it brings vendor reviews from different places and then verifies them with PGP signatures – that way, the buyers feel confident. Also, there’s a premium option for those who want extra advantages.
Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions. Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for. You’re also open to threats like end-to-end correlation attacks, so while Tor is a lot more secure and private, it’s by no means completely safe. Bitcoin is also supported, and there are multiple payment methods similar to Escrow, so both the buyer and the seller are protected during the transactions, and nobody is ripped off by the other party.



