The number of market-U2U and market-only buyers also drops as a consequence of operation Bayonet. However, compared to sellers, the drop is notably smaller, and the number of buyers rapidly recovers to previous values. Moreover, the number of multibuyers increases, which suggests a fast response from buyers to external shocks by trying to diversify their sources. Part of the operation to close the Monopoly marketplace, the arrests shed light on some scary facts about the Dark Web.
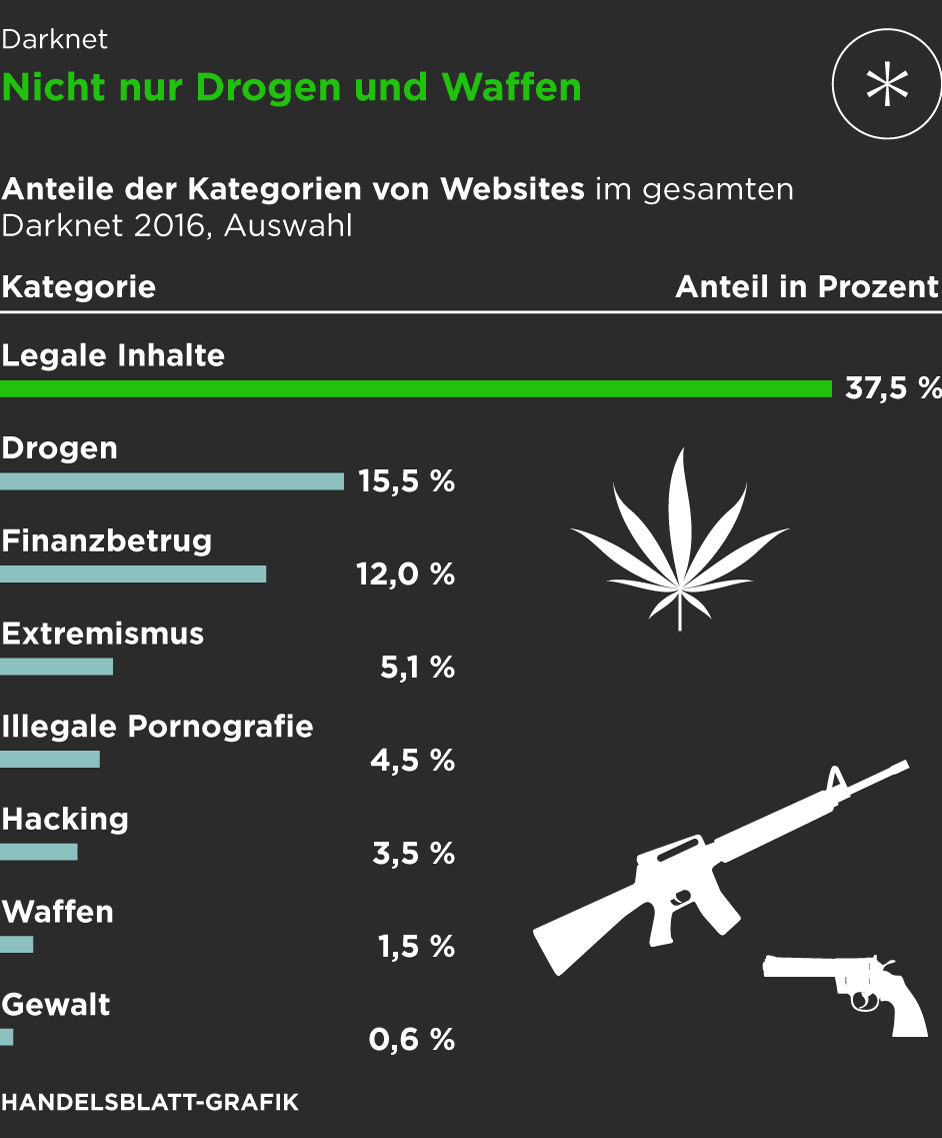
Dark Web Activity Breakdown By Category
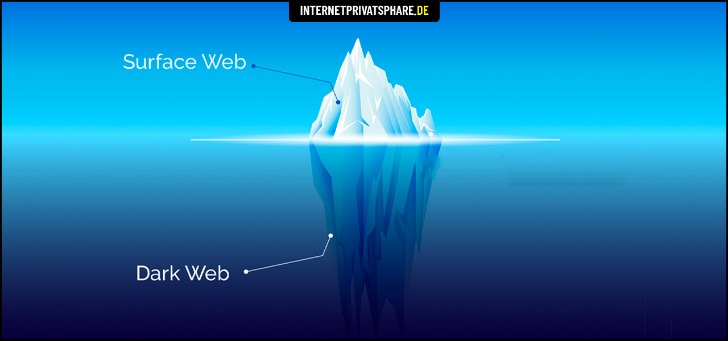
It includes things like private databases, email accounts, and online banking. The dark web is a small subset of the deep web that specifically focuses on hidden and illicit activities. Usually, criminals sell access to exploits and stolen data, but increasingly sites such as 0day.today are releasing more free material, from exploits to data dumps.
How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation
Specifically, to be classified as a multiseller, a user must be classified as a seller in at least two markets simultaneously. The multihomers play a crucial role in the ecosystem because they act as edges between markets. Hence we do not distinguish multisellers by the number of markets in which they operate.
Top 10 Best Dark Web Search Engines In 2025 Safe &
Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. A study, Into the Web of Profit, conducted by Dr. Michael McGuires at the University of Surrey, shows that things have become worse. The number of dark web listings that could harm an enterprise has risen by 20% from 2016 to 2019. Of all listings (excluding those selling drugs), 60% could potentially harm enterprises. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China.
Fraud And Hacking Services
Drug traffickers active on Nemesis sold fentanyl around the world, both on its own and surreptitiously laced into other drugs. These darknet markets are difficult to disrupt directly, but efforts to thwart customers of stolen data from using it offers some hope. We believe that advances in artificial intelligence can provide law enforcement agencies, financial institutions, and others with information needed to prevent stolen data from being used to commit fraud. This could stop the flow of stolen data through the supply chain and disrupt the underground economy that profits from your personal data. Dark markets provide a one-stop-shop for cybercriminals, offering a wide range of services such as hacking tools, stolen data, ransomware, and Distributed-Denial-of-Service (DDoS) attacks for hire.
The investigation uncovered a local criminal organization linked to a large international drug supply operation. Therefore, key actors in the ecosystem of DWMs may play important roles in broader criminal networks. In general, by understanding the operation of key players within the DWM ecosystem, our work highlights how appropriate strategies can be designed to counteract the online trade of illicit goods more effectively. Dark Web marketplaces are much like ecommerce websites on the Surface Web, but with one major difference — they mainly sell illicit and/or illegally obtained goods.
Dutch National Police Share Depth And Sophistication Of Genesis Market Identity Theft Operation
Many people see hacked information and stolen card data being sold on the dark web. For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. However, when it comes to darknet markets, the story is very different. Dark web marketplaces are mostly hubs for illicit goods and activities, posing serious risks to users and the wider community. Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown.
The market is especially well-known for providing access to freshly compromised data, often obtained from recent breaches and stealer logs. In 2022, for example, BidenCash was linked to the breach of over 1.2 million credit card records. One of the distinguishing features of Fresh Tools Market is its focus on providing up-to-date, freshly obtained tools and credentials. Founded in 2020, Cypher Market has carved out a niche on the dark web by focusing on cybercrime products.
Agentic AI-Powered, Intelligence-Driven Unified Cybersecurity Platform
- It operates in both French and English and has built a reputation for ease-of-use.
- There is a gray zone in which some sellers and buyers may not be easily distinguishable in transaction networks.
- As much as authorities work hard to shut down various sites, it shows what the dark web is capable of doing if left unchecked.
- Mega clearly dominated the realm of wholesale drug purchases, capturing 51.9% of that segment.
- Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers.
- Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums.
Future work may further extend the approach presented here, for example using machine learning methods to capture further behavioral regularities. Third, at any given moment we classify entities as either buyers or sellers. For example, in some cases, a seller in a given market may behave as a buyer in a second market or in the U2U network. This multi-role classification, to be implemented in future work, can help gain a more nuanced understanding of the ecosystem and the structure of the dark web supply chains.
Use Cryptocurrency For Transactions

Accessing darknet markets safely isn’t just about the tools you use — it’s also about the way you behave online. By following simple but effective OPSEC strategies, you can protect your identity, avoid scams, and reduce unnecessary risks. Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate.
Best Laptops For Cybersecurity Students In 2025 The U
However, owing to the difficulty of identifying relevant transactions, most studies rely on user surveys17,18 and data scraped from DWM websites19,20,21,22,23,24. In particular, these studies are based on user reviews which carry many inaccuracies, for instance, with respect to the time and value of the transaction19, that further compound error in other measures. Moreover, data scraped from the DWMs cannot assess the U2U transactions which account for the largest fraction of the total trading volume of the ecosystem13.
Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally. You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user.
The Tor browser is a privacy-focused web browser that allows users to browse the internet anonymously, including accessing .onion domains on the dark web. While the dark web is not illegal, mainstream awareness of the darknet is tied to the rise of the Silk Road, an online black market founded in 2011 by Ross Ulbricht. The Silk Road was especially known for its role in the online drug trade but was host to other illegal transactions until it was shut down by the Federal Bureau of Investigation in 2013. However, in recent years law enforcement have become more and more successful at shutting down these marketplaces, meaning that the vendors have to move to new areas. There have also been a number of exit scams from marketplaces with the admins closing down the site and taking the funds in escrow. Below you’ll find a table showing some of the major darknet markets Krixo has detected, their URLs, and their current status.