This historic takedown, led by Europol, resulted in the highest number of seizures in JCODE’s history. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge.

Not only do you need a dark web browser, you need a dark web search engine too. This search engine will get you to the sites you need, though you can also go directly to dark web addresses if you know what they are, as with standard URLs. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need.
The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across.

Both services have extremely sophisticated network of couriers with wide inventory of illegal drugs. According to the indictment, Parsarad, 36, of Tehran, Iran, launched Nemesis Market in or around March 2021. Nemesis Market operated on the dark web, a network that uses The Onion Router (TOR) to encrypt traffic and hide users’ Internet Protocol (IP) address. At its peak, Nemesis Market had over 150,000 users and more than 1,100 vendor accounts registered worldwide.
Keep Your Identity Hidden
The consequences can be lethal to those whose data is stolen, like identity theft, emotional distress, and even financial loss. Interestingly, the hackers don’t hide, but most of them even openly advertise what they offer on the darknet forums. Therefore, you can hire them to perform a task for you, from planting malware to hacking email accounts and even breaking into various social media accounts. Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring.
Top 10 Dark Web Markets
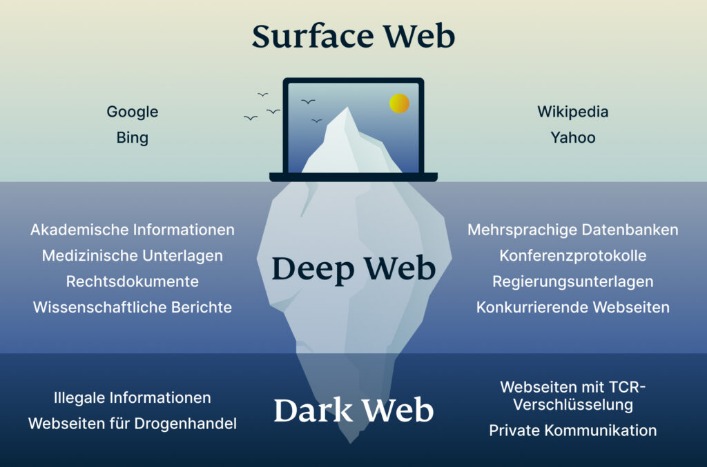
These pages come with extra protections for user anonymity and data security, and you need special software to access them—you can’t get at them through your normal web browser, like you can with much of the rest of the deep web. You can conduct discussions about current events anonymously on Intel Exchange. There are several whistleblower sites, including a dark web version of Wikileaks.
- The same report showed that cyberattacks on the healthcare industry grew by 86% in 2022 compared to the previous year.
- If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more.
- Once a buyer makes a payment, it’s usually held in escrow until they receive what they bought.
- It’s recommended not to use new alternative links as they could just be planned exit scams.
- Your online activity and communications remain private and secret on the dark web.
Hacking Services
Mega provides an automated exchange service and a built-in wallet to process cryptocurrencies. To further attract buyers of drugs from other underground communities, the actors behind the Mega frequently organize “Black Friday” discounts to stimulate the sellers, by doing so offering lower commission rates from their sales. As for RuTor’s ownership, this post by user ‘ER1VD4PC’ alleges that new owners of the forum are the Khimprom syndicate, “a large cartel, but alas, already operating under protection,” according to the translation. Such claims couldn’t be fully validated and should be treated with certain grain of salt.
Choose A Dark Web-compatible Search Engine
It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check. Darknet markets operate within this hidden space, often hosting illegal activity, while the deep web primarily consists of everyday private or password-protected content.
- Like other marketplaces, it also requires registration for new users and accepts payments in Monero.
- Additionally, Ransomware-as-a-Service (RaaS), where cybercriminals purchase ransomware kits to deploy attacks, has increased the frequency of ransomware incidents against SMBs.
- For the first time, FBI agents from all of the bureau’s field offices visited buyers to tell them about the overdose danger of pills sold online, which are often disguised to look like prescription drugs.
- Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them.
- Numerous vendors also sold hacking tools and hacking services through Hydra.
Treasury Designates Cryptocurrency Exchange Chatex
Regarding the impact of collaboration, as seen in Table 4, international collaboration accounts for 20.1% of the total. It has the highest TC/TP ratio of 13.7, while national collaboration accounts for 28.1% of the total and has a TC/TP ratio of 9.2. The top three sources for Darkweb research based on the number of citations (TC) are the International Journal of Drug Policy, Forensic Science International, and Addiction. These sources are all journals and have the highest TC/TP (citations per paper) ratios in the table, with the International Journal of Drug Policy having a TC/TP of 38.3 and Forensic Science International having a TC/TP of 32.3. According to Table 2, the top three research funders in this list are the National Science Foundation from the United States, the European Commission from Belgium, and the Japan Society for the Promotion of Science from Japan. Six of the top ten funding agencies are from the United States, and one is from China.
Set Up Tor Browser
The Tor network mandates that Tor clients (such as the Tor browser) can only access sites using the .onion TLD. However, these domains are not easy to distinguish, and are usually represented in long, often randomly generated alpha-numeric strings. Finding the correctly represented URL for a particular domain in the first instance can be a challenge. There are hundreds of marketplaces to choose from, each with their own set of communities, politics, and socio-economic motivations. I wont list them all here, as unfortunately not all survive long enough to outgrow the impulse of real-world influence and fallible human desires. Some get hacked, some get shut down by law enforcement, and some succumb to their own greed – whereby the operators ‘exit scam’ entire communities.
Hundreds Nabbed In Global Crackdown On Dark-web Drug Marketplace
We review and list tools and products without bias, regardless of potential commissions. He recommends verifying market employees carefully, and to weed out law enforcement infiltration through barium meal tests. Immigration and Customs Enforcement, in collaboration with Europol, the Joint Criminal Opioid and Darknet Enforcement Team, and various national and international partners, announced the results of Operation RapTOR May 22.
What Is The Cost Of Stolen Data On The Darknet Market?
Some of the sellers and their ads published at WayWay had references to another marketplace called Solaris. It also has its own forum with the same name for discussions between buyers and sellers. As of today, this marketplace is one of the most significant players in drugs sales in Dark Web. This market also features an ‘Other’ section where users can browse delivery services, as well as bank/SIM cards, passports and other identity documents, hacking services, web design, and laboratory equipment/precursor chemicals. Killnet has attracted a lot of attention because of past DDOS attacks against NATO, U.S. law enforcement, and multiple EU government agencies during the peak of war in Ukraine. It is not clear if this group may be state-supported or solely driven by their ideological motivation, or perhaps artificially created by foreign governments considering ongoing geopolitical tensions.
Also, while this huge portion of the internet has a reputation as home to nefarious activities like hacking and drug trafficking, it also harbors legitimate activities like journalists and whistleblowers. Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online. Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft.
Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download. The authors declare that they have no known competing financial interests or personal relationships that could have appeared to influence the work reported in this paper.



