The information you enter will appear in your e-mail message and is not retained by Tech Xplore in any form. In the admin panel you can create categories, respond to vendor applications, disputes or create news. Feedback score is basically percentage of positive feedback and Trust rating can be Very Low, Low, Average or High (Unproven if the user has less then five feedbacks). When an user registers, he receives an unique mnemonic that can be used to reset the password.

Russians On The Darknet Part II: Marketplaces & Forums
It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. RuTor has been an active Tor hidden service since 2015 and has quickly established itself as a reliable information resource for Russian hacking, darknet education, and project collaboration. RuTor’s landing page has several distracting advertisements at the top of the site similar to the previously popular RAMP marketplace. Both MEGA and Hydra hidden services emphasize trusted vendor-buyer relationships before the market will facilitate the crypto-transaction and goods exchange. For example, on Hydra, before an order from the buyer is processed, the vendor and buyer must communicate and trust each other. The market even offers a “transaction chat” platform to communicate securely about the order.
Outdated browsers, wallets, or VPN apps often contain vulnerabilities that attackers can exploit. At the same time, avoid unnecessary downloads or opening files from unknown sources — many contain hidden malware. Staying cautious with software and limiting what you expose yourself to are critical steps in darknet market safety. Accessing darknet markets safely isn’t just about the tools you use — it’s also about the way you behave online.
Torrez Darknet Market
With a trusted onion market list, however, you gain the confidence of knowing you are connecting to legitimate dark markets rather than malicious copies. These charts present consumption as circles whose size is a function of the percentage of the national population engaging in the use of that particular drug. The goal of this method is that no one party has enough information to take funds from these P2SH addresses. This means PGP encrypted messages in the database can’t be decrypted, even if a full copy of the server is obtained.
Most Popular Darknet Market
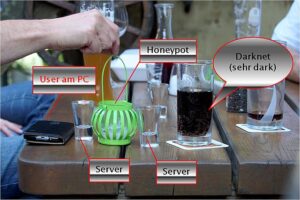
With both the copyright industry coming down on the DRM circumvention and copyright infringement groups, and government alphabet soups (FBI, DOJ, SEC, etc.) coming down on the virus trade, these groups began going further underground. They found that to minimize risk, they would need to utilize end-to-end anonymity software, thus fostering a new iteration of digital black markets on a network colloquially termed the “dark web.” By B Leclerc 2021 Cited by 3 Crime script of CSAM offenders operating on the darknet A crime script analysis of the online stolen data market. Contrary to best darknet market australia other darknet markets, Infinity Market only supports Bitcoin as a the different wallet, you will need to import your redeem script into it. By J Brosus Cited by 70 the proportions these categories represent on darknet markets. Through a Python script to extract its title, price and classification within the.
Cryptocurrency Wallets For Safe Transactions
With the increased reliance on computers and the Internet, the market to exploit it grew as well. This began with tools that generally were more precisely targeted – utilities like Back Orifice and Sub7 – intended for sale to users called “script kiddies” (a pejorative term meant to indicate their newbie level in many regards). With the growth of websites built by Internet startups and enthusiasts, closed-source tools were developed and sold to allow script kiddies and beyond to scan, analyze, and attack those websites. In a way, they were similar to modern automated web security scanners — except rather than searching for both known and unknown vulnerabilities and providing suggestions to fix them, they searched for specific web applicion vulnerabilities and provided utilities to viciously exploit them. Some even granted some time-shared access to botnets like ZeuS to bludgeon websites with unrelenting DDoS or focused Layer-7 attacks, like authentication brute forcing or comment spam. Of course, these tools eventually found themselves on free file sharing platforms like KaZaA and LimeWire, but not before they found plenty of sales on online black markets first.
Utilizing a bulletin board format similar to Wayaway, RuTor has established sections for Vendor Shop Fronts, Security, and News. The cryptomarket portion of RuTor is tightly controlled by the site administrator who must be contacted before submitting a deposit in a user’s market wallet. Most centralized marketplaces have an automated system for all market crypto-wallet deposits and withdrawals. RuTor has extensive threads covering cybersecurity related news, corporate data breaches, and technical tips and techniques for network infiltration and tracking. While DarkOwl generally avoids engaging in or commenting on speculative darknet drama, there are several things about the re-emergence of AlphaBay and DeSnake that don’t add up. While DeSnake very well could be legitimate, the sheer fact the authorities confiscated the market’s servers and Cazes’s unencrypted laptop should bring significant suspicion whether this new darknet marketplace is legitimate, or simply another covert law enforcement operation.
It operates by utilizing a network of anonymous relays that traffic hops through. In fact, over one-third of all TOR traffic consists of dark web black market traffic, including drugs, illicit goods, fraud, and much worse. From there, we learn how digital black markets began pretty much with the beginnings of the Internet itself. Starting with, and for the longest time still existing on decades-old Internet technology, we explore the slow, progressive evolution on this platform.
Uk Darknet Markets
By running the command below, we filter out all the unnecessary features from the item and feedback files and merge them to create preprocessed_alpha.csv, preprocessed_dreams.csv, preprocessed_silk.csv, and preprocessed_agora.csv files in the data directory. Then, we load these files for all our future experiments as input to our scripts. When user purchase any item there is a fee (that can be configured) and automated escrow.
Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. In 2023, the dark web attracted an average of 2.7 million daily users, with Germany now leading as the country with the highest number of Tor users, surpassing the United States for the first time in years. Goal of Tochka is to provide reliable software for next-gen darknet operations, while staying transparent, free and secure. He recommends verifying market employees carefully, and to weed out law enforcement infiltration through barium meal tests. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
Systems like Bulletin Board Systems, Usenet, and later websites on the budding World Wide Web provided a home to these activities. We briefly explore why sellers (and buyers) take the risk, in spite of increased penalty and raids. Pideeco reserves the right to remove any offensive, inapropriate nor discriminatory content. More specifically, Harmon failed to file suspicious activity reports for transactions within dark web markets, as required darknet market sites by the Bank Secrecy Act.
Russian Market
Even comedian Mitch Hedberg joked nearly two decades ago that his postal delivery guy was unwittingly a drug dealer – “and he’s always on time.” While a market is an economic institution where tangible currency in some form is exchanged in trade for goods or services, a black market is similar, but involves either the currency exchange itself or the goods or services being traded being illegal. This is done typically to circumvent regulatory powers, avoid detection, or simply to obtain illicit or illegal goods. To minimize risks when exploring darknet markets, you need the right set of tools. These tools protect your identity, secure your connection, and make it harder for malicious actors to track or scam you.
Dark Web Marketplaces
DeepOnionWeb is the best source for official darknet market links, darknet related news, and fresh alternative deepweb Onion List & Availability Status. Trade on several ofthe dark web’s illegal markets has boomed since RsClub Market lists weapons as well as drugs and other illegal goods. Examples include the sale of high-quality products with low risk for contamination (including lacing and cutting), vendor-tested products, sharing of trip reports, and online discussion of harm reduction practices.
Reddit Darknet Market List 2021
PGP ensures that messages and sensitive instructions are encrypted and cannot be intercepted. Using unique keys for each vendor or market prevents leaks and protects your communication from third parties. It has a bidding feature, with new batches of stolen data being frequently added. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. If you ever decide to explore the dark web, protecting your identity is crucial. Ransomware and cryptocurrency-based crimes saw a significant increase in 2023, with a nearly $176 million rise compared to 2022.

Software Requirements
- To expand their reach, some marketplaces established parallel channels on Telegram.
- These havens of anything-goes became the go-to for anyone wishing to participate in anything with minimal fear of being caught, coming with the unsurprising caveat of often being very seedy, immoral, and even hostile.
- Communities like this IRC network deeply valued good reviews of sellers to establish credibility and trustworthiness.
- In fact, the attacker need not even have much of any technical prowess – just a basic, high-level, abstract understanding of web attacks.
- You can retake everything except illegal porn, professionalism, hitman-services, ergo speechless chemicals and allergies.
These phishing sites often look identical to the real platforms, making it difficult for newcomers to tell the difference.Using verified onion links is the safest way to avoid these traps. Reputable onion site lists and darknet markets directories regularly check the uptime and authenticity of each market, ensuring that only real, working links are provided. By relying on verified sources instead of random links from forums, you minimize the chance of losing funds or compromising your identity.Accessing the dark web without this precaution is like walking into a minefield blindfolded.
Extreme momentary fluctuations like “flash crashes” were known to happen occasionally, too, such as one case where the value went from $700 to $100 back to $655 in a single morning. Lately, the value of BTC has remained around on average $250 USD per BTC for all of 2015 thus far. In 2008, an entity that went by the name of Satoshi Nakamoto (either a single person or team of people pretending to be one) released the Bitcoin payment system.