Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. This includes using an anonymous browser like Tor, a VPN to encrypt your connection, an antivirus for protection against malware (we recommend TotalAV), and generally being careful not to reveal personal information. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page.
Exit Node Caution
Silk Road’s takedown in 2013 fueled both fear and fascination, marking a high-profile enforcement milestone. However, it didn’t close the chapter on the dark web but, instead, opened the gates for many imitation sites. The subsequent captures of dark web operators resulted in a constant cat-and-mouse game, further embedding the idea of lifestyle communities within the web’s shadows. A pivotal moment in the history of the dark web came in 2002 with the introduction of Tor (The Onion Router).
Market Features
The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki. It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity.
Activities
Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Site operators can also submit their own .onion sites for indexing. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google.
Bitcoin Wallets
- Noteworthy features included a lack of withdrawal or deposit limits, a 5% fee for sellers (with no fee for buyers), and private listings for custom orders or discounts.
- With over 20 years of experience in cybersecurity and marketing, Ben has held leadership roles at companies like Check Point, Cognyte, Cylus, and Ionix.
- Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously.
- Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity.
- Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023.
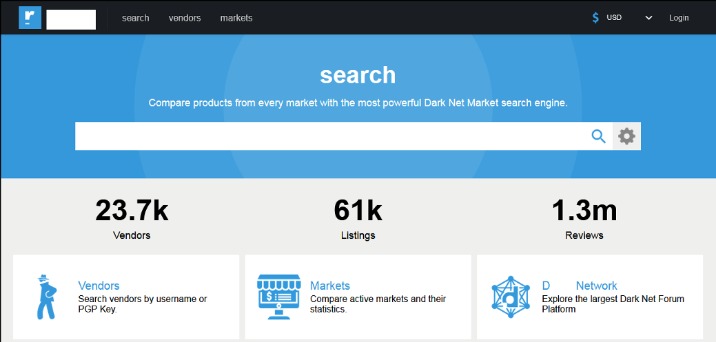
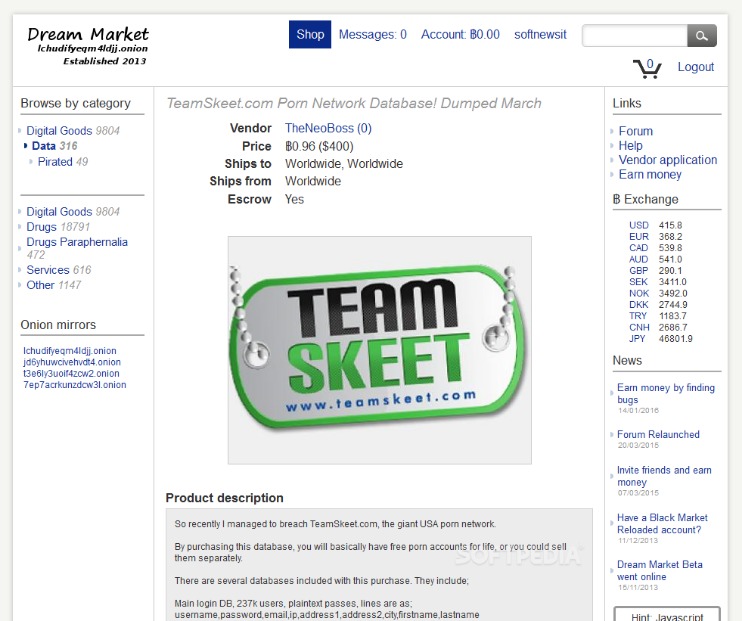
The second category consists of data stores, which specialize in stolen information. In 2023, the dark web attracted an average of 2.7 million daily users, with Germany now leading as the country with the highest number of Tor users, surpassing the United States for the first time in years. Over the years, dozens of large DNMs have been established and eventually shut down by law enforcement, including AlphaBay, Dream Market, Wall Street, and, most recently, Hydra. DNMs are located on the “darknet,” which is unreachable on standard internet browsers like Chrome, Firefox, or Safari because the darknet is unindexed. There are certain sites on the darknet (and on clearnet) which attempt to manually track and publish sites on the darknet, but common browsers do not link directly to darknet.
Does The CIA Have An Onion Site?
Unlike other search engines, it does not collect or share web activities and personal data of users. Naturally, this makes the dark web a breeding ground for illegal activity. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. The deep web is the part of the internet you can’t access through search engines like Google and Bing.
The Cyber Express News
We analyze how digital marketplaces operate in the United Kingdom, Germany, London, and throughout the EU, covering both technical and legal aspects. Its .onion site provides an additional layer of privacy and security for users accessing their Bitcoin wallets or exploring transaction data, especially useful in regions where cryptocurrency sites might be monitored or blocked. Blockchain even has an HTTPS security certificate for even better protection.
These services can potentially log your IP address or expose your information through various means, undermining the benefits Tor offers. While some of these markets were shuttered by law enforcement agencies – some took the easy way out with exit scams. Here are some of the now-defunct dark web markets that were notorious for cybercrime. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in.
It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. RiseUp is a top dark web website that offers secure email services and a chat option.

Experience The World’s Most Advanced Cybersecurity Platform

Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Also, you must log in or have a specific IP address or URL to access the deep web content. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa. The dark web isn’t just one sketchy marketplace hiding in a corner of the internet; it’s more like a messy, unregulated community with everything from freedom fighters to full-blown cybercriminals.
The site would be reinstated in November,6 with a revamped user interface, and remains active as of September 2025. It became known that the cause of the outage was a server failure, according to HugBunter,6 despite rumorsby whom? concerning a potential compromising from a third party or law-enforcement authority. Archetyp Market emerged in 2020 as a major player in the darknet’s illicit drug trade, quickly gaining notoriety for its vast inventory and user base.
For added security, consider using a reliable VPN in conjunction with Tor. A VPN can mask your Tor usage from your Internet Service Provider (ISP), but be cautious — some VPN providers keep logs that could compromise your anonymity. Downloading files from the Tor browser can compromise your anonymity. Malicious files might bypass Tor’s security, giving away your real IP address. If you must download files, ensure you’re using a separate, secure environment — such as a virtual machine.
Ares Market Onion Products
Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web. To look at it in a different way, it makes up between 90% and 95% of the internet. The dark web and the deep web are often used interchangeably, but they’re two distinct concepts. In short, the major difference between them is that the deep web contains internet content that you can’t find through search engines, while the dark web is a hidden network that requires a special browser to access. A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity.
Given the darknet’s infrastructure, which is hidden behind onion routing, the darknet attracts sites whose proprietors want to remain anonymous. The most common darknet software is the free and open-source Tor, short for the Onion Router. The software was developed in the mid-1990s to protect U.S. intelligence communications online and is used in conjunction with virtual private networks (VPNs). Tor software, in conjunction with the user’s preferred VPN, conceals the user’s location and IP address and is implemented through layers of encryption, akin to the layers of an onion, from which the service derives its name. While some competing darknet softwares are similar to Tor browsers, they typically exist for different purposes. For example, the network dn42 exists to help users form connections and networks rather than to preserve user anonymity.