Conor Brian Fitzpatrick, 22, of Peekskill, New York, was resentenced today to three years in prison for...
counterfeit
Many malware take advantage of this vulnerability to launch an attack. Therefore, you can prevent this exploitation...
Purchases through links on our pages may yield affiliate revenue for us. We review and list tools...
Finally, we are ready to assist you with your financial needs both small and large scale. It...
It’s a user-only marketplace, meaning you need to register to enter. During our tests for the research,...
They can be used for financial crime, identify theft, as well as counterfeit goods. Counterfeiting can range...
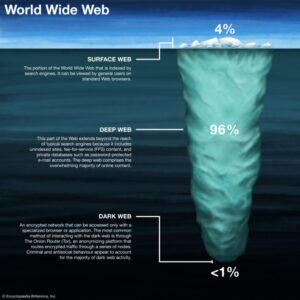
For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who...