Figure 2 shows how many products (not just counterfeits) were offered across all markets over time. The volumes shown are monthly and contain all available products on the dark markets. For most markets, the data range between January 2014 and September 2015, but the data for the market Alphabay extends to January 2017. Evolution and Agora offered the most products, followed by Alphabay, Abraxas, BlackBank Market, and Cloud 9. The remaining markets seem to have offered only a minimal number of products and for shorter periods.

Hundreds Nabbed In Global Crackdown On Dark-web Drug Marketplace
- The advantage of a holding price is that vendors can keep showing customers what was sold and what might be coming back in stock.
- The .gov means it’s official.Federal government websites often end in .gov or .mil.
- For example, the number of routinely checked containers at major ports in Genoa (Italy), Melbourne (Australia), Montreal (Canada), New York (USA), and Liverpool (UK) together only account for 2–5% of all traffic (Sergi, 2022).
- “Our study highlights the fact that illegal tobacco trafficking is essentially carried out outside the Web because the normal distribution networks have been in place for several decades,” said Décary-Hétu.
- In Grand Theft Auto Online, players who purchase warehouses and garages for illicit cargo and stolen cars can buy/steal and sell them through trade on the “SecuroServ” syndicate website.
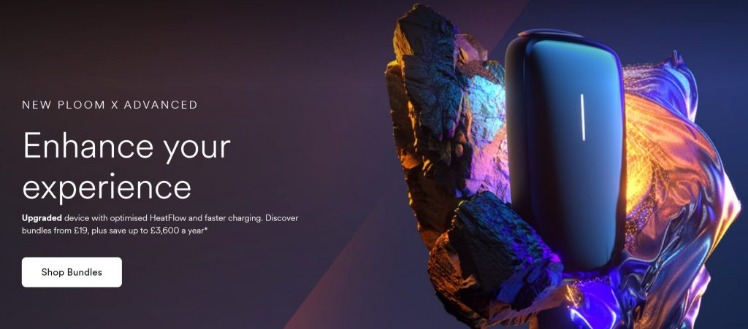
The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. In contrast to the differences observed for counterfeit products seized at borders and offered on dark markets, product origins seem to match better across data sources. For example, between 2014 and 2016, seized goods mainly originated from China (55%) and Hong Kong (26.2%) (EUIPO, 2019; OECD/EUIPO, 2019). However, seized goods also originated from the United Arab Emirates (3.8%), Turkey (3.1%), Singapore (2.8%), Thailand (1.4%), India (1%), and other countries (each with less than 1%) (OECD/EUIPO, 2019). In contrast, for the dark markets, counterfeits were either not explicitly offered from these countries (e.g., Singapore, Thailand, India), or they accounted for less than 1% of the listings.
Tor2door Market
Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance. Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details.
Featured Publications
As Hollis and Wilson (2014) discuss, addressing the problem in cases where companies have been misled would involve improvements to guardianship in risky parts of the supply chain. Companies could be provided with information about which products are affected and from which country they originate to facilitate their efforts to identify risks in their supply chain. Such implementations could include raising employee awareness of the affected products, implementing reporting mechanisms, or introducing additional validation checks for particular product types for specified periods of time. To aid in this activity, dark net market data—searchable by brand—could be made accessible to companies. Since product information is quite detailed, an implementation with up-to-date darknet market data is feasible.
In repressive regimes, darknets play a vital role in enabling free speech and access to uncensored information. Tools like Tor are used to bypass government-imposed firewalls and surveillance, ensuring open communication. The significance here is the preservation of civil liberties and the right to information. Businesses operating in such regions may need to adapt to the technical challenges and risks posed by using darknets for legitimate purposes.
Activities
Both Metals and Pharmaceuticals show high standard deviations, which can be attributed to a few very high-priced listings. For example, “28 g PSEUDO SPEED” for $2000 or “Lot of 10 High Quality Counterfeit Gold Bars” for $5799. By comparing our measures of the types of counterfeits to goods seized at borders, we can identify how products differ and discuss possible contributing factors to those differences. Based on a report by OECD/EUIPO (2019), which summarizes findings regarding seized counterfeits between 2014 and 2016, we see that not all categories represented on dark markets are also present in seized goods (Table 5). Also, the distribution of counterfeits found on dark markets and seized products varies greatly. In addition, sunglasses, handbags, and other accessories, which make up around 10% of counterfeits on dark markets, are not listed individually in the report but are grouped within headgear (1.5%), miscellaneous (0.4%), and articles of leather (13.4%).

Dark And Surface Market Prices
As a result, threat actors have migrated elsewhere, including to forums like “RuTor,” decentralized Telegram-based shops, and even switching to offline transactions for physical commodities like narcotics. 2Easy is a quickly-growing dark web marketplace that’s based around a similar concept as the Genesis Market. The market now has an established reputation among cybercriminals, which means that any stolen credentials for sale on there are likely to provide valid access to systems, services, or apps. Lastly, we summarized counterfeit prices for each category (Table 7), estimated vendor sales volumes (Table 8 and Fig. 5), and examined the price differences of products offered on darknet markets and the surface web (Table 9, Fig. 6). They accounted for 3.3% of worldwide trades in 2016, having an estimated value of $509 billion in the same year.
Easy Steps To Access Dark Web On Your Phone Safely In 2024
“These networks either source legal products sold at lower cost in some countries for resale in countries where tobacco taxes are high, or they source counterfeit or illegally manufactured products,” Decary-Hétu said. Using automated Datacrypto software he developed himself, Décary-Hétu scoured the dark Web in the summer of 2018 to see if resellers of tobacco products had diversified their activities. Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware.
While provincial police in Quebec and Ontario are doing what they can, they don’t have the resources to keep up with the ever-growing market. In other words, a clear plastic ziploc bag of 200 unmarked cigarettes should be a dead give away.
Not long after the news broke out about the Hydra takeover, a new darknet spot appeared to be competing for first place. In 2013, Silk Road founder and darknet drug emperor Ross Ulbricht, AKA Dread Pirate Roberts (DPR), seemed convinced that his website was destined to become the catalyst for a revolution. After all, his site linked nearly 4,000 drug dealers around the world to sell their wares to more than 100,000 buyers, and could you get you anything from falsified documents to heroin — even a rocket launcher. Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum.
- OCDETF identifies, disrupts, and dismantles the highest-level criminal organizations that threaten the United States using a prosecutor-led, intelligence-drive, multi-agency approach.
- For example, between 2014 and 2016, seized goods mainly originated from China (55%) and Hong Kong (26.2%) (EUIPO, 2019; OECD/EUIPO, 2019).
- Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats.
- In 2013, a polyglot group of programmers and hackers, under the leadership of an eccentric fifty-three-year-old Dutchman named Xennt, moved into a Cold War-era bunker near the picturesque town of Traben-Trarbach, in the Mosel Valley.
- While possible shipping destinations are included in the listing data, we did not analyze these as most destinations are listed as “Worldwide” or “Undeclared”, providing only limited information.
Traceability of genuine products within a supply chain would also fall within that category, as it increases the efforts needed to counterfeit them, which could be technologically facilitated (Gayialis et al., 2022). Alternatively, the offenders’ rationalisation for committing a crime could be challenged by removing possible excuses for their actions. Removing excuses includes approaches such as setting up rules or posting instructions to reduce ambiguity in situations that can be exploited.
Is It Illegal To Access The Darknet?
It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data. The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime.
Dark Web Marketplaces
Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange. Among a suite of objections, the company claimed denicotinisation, reduced availability of tobacco, and the introduction of a smokefree generation would lead to serious unintended consequences. These included a tobacco black market that would fuel “drug trafficking, money laundering and other nefarious activities”. For example, some custom orders might have similar descriptions as other counterfeits. Besides custom orders, the category “Other” also included guides, instructions, counterfeit art (e.g., paintings), or cars.
Fraud And Counterfeits On Dark Markets
In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described. Accessing any darknet marketplace is dangerous because it is known to be a hub for illegal trade. In addition, several fake websites impersonate the famous dark net marketplace to obtain your financial and personal information and use it for malicious purposes.