Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web. Quality and validity of the data it provides justify its higher cost over other marketplaces. The platform’s popularity continues to grow, attracting both new and returning customers.
Hacking And Cybercrime Sites
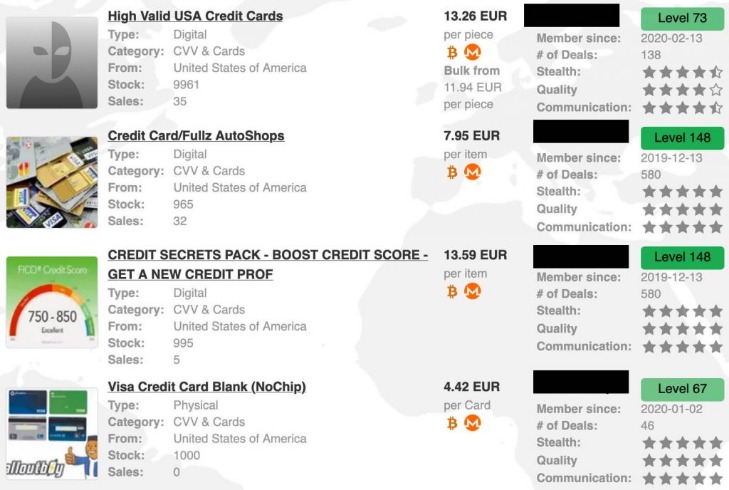
Dark web vendors sell stolen personal identifying information (PII), stolen credit card numbers with verification codes, fraudulent bank accounts, and fraud software. There are thousands of websites on the dark web, many—but not all—of which are illicit marketplaces selling stolen personal data. Learn more about the kinds of sites that can be found on the dark web and how you can access them. Then, use a powerful identity theft protection tool, like LifeLock Standard, to help find out if your personal data is leaked on the dark web. In the past year, the dark web data market grew larger in total volume and product variety, so as supply grew, most prices plummeted, according to Zoltan.

Security Vulnerability
Once installed, it grants hackers full access to the machine’s capabilities. With some real information and some expertise, they can easily produce a collection of fake, authentic-looking documents. As a consequence of this, likely fewer crypto trading accounts and wallets were available for hackers to target.
In 2020 alone, American consumers lost more than $56 billion to credit card fraud and identity theft scams. With fraud driving massive profits for scammers and cyber criminals, a large underground economy has emerged to supply the most daring, aggressive, and organized fraudsters with the tools and data they need to keep their scams running. The dark web is a hidden part of the internet where users are anonymous and can access illegal marketplaces and hacking forums and partake in illicit activities. In some cases, it’s also used for private messaging, cybersecurity training, whistleblowing, and other legitimate uses.
Credit Card Monitoring Alerts
Carders tend to target specific sites that don’t have VBV or other protections against fraud. For fledgling criminals who don’t know how to use stolen credit cards, there are plenty of free and paid tutorials for carding on the dark web. In addition to these types of listings, there are other free tools usually available on credit card sites. These tools include for example different types of checkers, which assist threat actors in verifying whether the stolen card information they possess is valid and can be used to make unauthorized purchases.
Since then, BidenCash has continued to operate using the “dumping” method. This involves adding daily listings of stolen credit card details to the site and periodically dumping large amounts of stolen credit card details at the same time. This post will discuss deep and dark web credit card sites, specifically the top illicit credit card shops. Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records.

Dark Web Monitoring And Identity Theft Protection At Your Fingertips
Comparitech researchers analyzed listings across 40+ dark web marketplaces gathering data on how much stolen identities, credit cards and hacked PayPal accounts are worth to cybercriminals. This becomes particularly explosive when it comes to login credentials for payment services like PayPal, which are directly linked to bank accounts or credit cards. In the current incident, a data package is circulating under the title “Global PayPal Credential Dump 2025.” It contains millions of login credentials – and could affect users worldwide.
- Hacked PayPal accounts have been increasing in value since the start of the pandemic.
- Monitoring the dark web can help enterprise security teams anticipate and counteract upcoming cyber attacks, or detect evidence of prior attacks and take action to minimize the damage and prevent further distribution of stolen data.
- Foss adds that the use of ransomware is also popular among retail-focused cybercriminals.
- We’ve seen dark web vendors listing everything from pirated eBooks and software to counterfeit electronics and fake gold bars.
- A single hacked account can open the door to identity theft, due to password re-use and the wealth of personal details stored within that can be exploited.
- The sad truth is with the growing supply of personal information on the dark web, the likelihood and occurrence of devastating hacks increase every day.
Dark Web Price Index 2022
Other dark web vendors are simply low-level fraudsters and opportunists, selling things like phone-verified Paypal and Cash App accounts or sharing their Netflix login information for a one-time fee. Dark web vendors are merchants who sell illicit goods and services in underground marketplaces hosted on the dark web. With the sheer quantity of data available for purchase, they need to play the numbers game, and if you don’t protect yourself, you’ll be the one paying the price. Adopting a few simple rules and habits will make it harder for hackers to get your data and, in doing so, take yourself completely out of their crosshairs. Next, we dive into the detailed trends for eight categories of fake, hacked, or stolen data and physical documents. But because PayPal account details are the most popular among payment processors, they are also relatively cheap.

Of Employees Will Shop On Mobile Phones This Holiday Season
Therefore, the probability of being hacked is unpredictable but on the rise unless you take measures to protect yourself. While these guidelines may appear complex and bothersome initially, they will become second nature once you become accustomed to them. This is when you will develop a crucial sense of cybersecurity both online and in everyday life. They are often poorly mounted, so if the keypad appears to be off-center or wiggles slightly, stop using it and inform the bank. The DDoS attacks listed below are characterized by their target, number of access requests, quality, speed, and duration.
Shuttered Dark Web Marketplaces
Here are some of the now-defunct dark web markets that were notorious for cybercrime. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. Never log in with your real name or reuse passwords from other accounts. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info.

As with credit cards, the location of the victim whose information is up for sale has a significant influence on price. Japan, the UAE, and Europe have the most expensive identities at an average of $25. The data posted on these online illicit shops is a goldmine for threat actors who are looking to commit financial crimes. It provides them with valuable information needed to carry out a variety of attacks.
Category #2: Details Needed For Physical Fraudulent Use
Amber Bouman is the senior security editor at Tom’s Guide where she writes about antivirus software, home security, identity theft and more. She has long had an interest in personal security, both online and off, and also has an appreciation for martial arts and edged weapons. With over two decades of experience working in tech journalism, Amber has written for a number of publications including PC World, Maximum PC, Tech Hive, and Engadget covering everything from smartphones to smart breast pumps.