Founded in 1998 as Ixquick.com, we later changed the name to Startpage.com. At Startpage.com, they take into account the privacy dangers of recording people’s search behavior, and given their team’s strong convictions about privacy, they decided to act accordingly. And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics. Great life advice, but it’s even more valuable where the darknet is concerned.
How Do I Access Onion Sites?
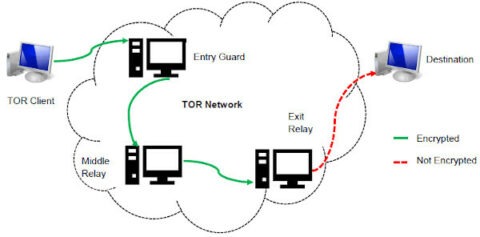
Law enforcement agencies, intelligence communities, and cybersecurity professionals often maintain a presence on the dark web to monitor, investigate, and potentially apprehend individuals involved in illegal activities. Internet service providers may also be suspicious of Tor usage and might monitor traffic patterns, even if they cannot see the content of the encrypted communications. Furthermore, sophisticated actors may employ traffic analysis techniques or target vulnerabilities at Tor’s entry and exit nodes in attempts to deanonymize users, although this is generally considered difficult. Therefore, while Tor provides a strong layer of privacy, it is not an absolute shield against surveillance, and users should remain aware of this possibility.
Liked It? Share It!
As long as you are not looking for anything illegal in the real world, it’s perfectly legitimate to use the dark web to find whatever you need. Nevertheless, the dark web is home to certain disturbing and illegal content you’ll never find on the surface web. It’s not that you can’t find prohibited content on the surface web – it’s just harder to look for it, as Google or Bing filter the most harmful sites. If you stumble upon any websites that seem illegal, just close the window. It offers a Reddit-like interface, where you can learn everything you need to know about darknet websites and spotting the real from the scammers. For the record, there are more scam sites for every genuine one, and it’s good to have a discussion forum about this.
How Do Onion Routing And Tor Work?
This traditional search engine is also compatible with the dark web and can help you find dark web websites. Swiss based ProtonMail is an encrypted email service that is quite popular with the cryptocurrency community. It’s a paid service, and while it’s extremely secure you will need another email address to sign up, which can leave traces of your true identity without you realizing. Deutsche Welle (DW) is a German state funded news organization that reports on worldwide topics and events. In order to avoid censorship of their content, they’ve created a .onion site to ensure it’s accessible for all.
Download Tor

To review security settings, click on the onion logo in the top left and select “Security Settings”, which will bring up a slider offering a choice of the default of standard, or safer and safest. In “safer” mode, JavaScript is disabled on HTTP sites, some fonts are disabled, and all audio and video won’t run automatically, you’ll have to click to play. Slide up to the “safest” level, and as well as those settings, JavaScript is disabled on all sites. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details.
Well-known news websites, such as ProPublica, have launched deep websites. Meanwhile, Facebook also offers dark web access to their social network. However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces.
What Is The Tor Network? The Anonymous Internet, Explained
After AlphaBay closed, Abacus Market took its place as the world’s largest underground darknet marketplaces. Abacus Market quickly rose to prominence by attracting former AlphaBay users and providing a comprehensive platform for a wide range of illicit activities. This search engine’s mission is to be leaders in providing services on the deep web, protecting the anonymity of each user.
How To Protect Your Identity While Browsing The Dark Web
The website has received six Pulitzer Prizes for its grassroots-based journalism. Accessing it through an onion link is much more convenient if you’re unable to directly view it on your screen. In order to use the Tor Browser and connect to the Tor network, you need a device that runs on Windows, macOS, or Linux.
Additionally, there’s a unique reward system based on cryptocurrencies, and you can also use the built-in crypto wallet. It can also block any ad targeting and keep your searches and browsing activities private. While the Tor Browser is the only one with access to the secure network of the same name, there are other viable choices on the market that also help keep you safe on the internet. In addition to the privacy solutions, when you download the Tor Browser, you also get a batch of security-oriented features. These include things like NoScript for blocking harmful scripts or HTTPS Everywhere, which forces pages to use the secure protocol over HTTP whenever possible. Instead of trying to route any particular app over Tor, why not route all your internet data over the Tor network?
There’s no broad consensus on dark web safety, but you at least need to use Tor and VPN together. Once you have those, there are several ways to tunnel through the dark web. If you now open whatismyipaddress.com in another browser, such as Edge, you will see that you are using a different IP address in the Tor browser. A look with the Tor browser at a darknet directory such as the uncensored Hidden Wiki reveals that seemingly anything goes on the darknet. So you’ve downloaded the Tor browser to your device and now you’re ready to start exploring the dark web? Before you do anything, it’s important to ensure that your browser has the optimal configuration of settings to ensure you don’t leave yourself vulnerable to exploits or becoming de-anonymized in some way.
Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa. Hence, you never know when a popular .onion site is going to vanish, or even die. Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links. The good news is that the platform will not see what you copy/paste.
- And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.
- The Tor Browser stands as a specialized tool in the realm of internet navigation, designed to grant users enhanced privacy and anonymity while online.
- Many users suggested that there is another authoritative website with similar functions, namely tor.taxi.
- As a crucial security measure, the Tor Project strongly advises users to verify the digital signature of the downloaded Tor Browser file, regardless of the operating system.
- While the dark web is not illegal, mainstream awareness of the darknet is tied to the rise of the Silk Road, an online black market founded in 2011 by Ross Ulbricht.
Therefore, the dark web should not be considered synonymous with the entirety of the unindexed internet; rather, it is a specific, intentionally hidden segment prioritizing anonymity and privacy. Privacy experts warn that law enforcement, intelligence services, and malicious hackers run their own exit nodes for exactly that surveillance purpose. It’s critical, then, for Tor users to only visit HTTPS-protected websites to ensure that the information that passes between the browser and the site remains encrypted. The Tor network understands these addresses by looking up their corresponding public keys and introduction points from a distributed hash table within the network. It can route data to and from onion services, even those hosted behind firewalls or network address translators (NAT), while preserving the anonymity of both parties.
Which Is The Best Laptop For Cyber Security Course?
Always remain vigilant about the risks involved with risky behavior, even when browsing through Tor. Disable JavaScript in Tor until you trust the site you’re visiting. Go to the security settings and set the security level to “Safest” to minimize potential vulnerabilities. Downloading files from the Tor browser can compromise your anonymity. Malicious files might bypass Tor’s security, giving away your real IP address. If you must download files, ensure you’re using a separate, secure environment — such as a virtual machine.



