With support for multiple cryptocurrencies and a trusted escrow system, DrugHub stands out as a reliable destination for privacy-focused online trade. The dark web, an even more puzzling sublayer, exists within this hidden world. It’s designed as an environment to elude detection, where site owners and visitors hide their identities. And while the dark web isn’t synonymous with illicit activities, it’s undeniably the breeding ground for the internet’s black markets, hacker forums, malware vendors, and other illegal activity. It offers access to hacked bank accounts, credit card data, and cryptocurrency laundering tools.
How To Get The Tor Browser
The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search. Archetyp was shut down as a result of actions carried out by law enforcement between June 11 and 13. Authorities in Germany, the Netherlands, Spain, Romania and Sweden participated in the operation that targeted people and technical infrastructure. This feature is satisfied when \(\phi _i(t) \le \tau\), where \(\tau\) is the maximum value of mean interevent time. For each entity, we keep track of the cumulative values of the six features for each transaction performed by the entity over time. To be classified as a seller, an entity must simultaneously satisfy the six feature threshold criteria, as follows.
Supporting Illegal Activities Unknowingly
It is legal to host sites containing illegal activity, so long as the host is unaware of the content and does not actively assist the site’s owner in illegal behavior. A German police unit in Mainz spent about five years spying on Xennt, using digital and phone taps as well as undercover officers—including a man employed as a gardener at the bunker complex. In September, 2019, Xennt and most of his lieutenants were arrested in a nearby restaurant, as German police made a spectacular raid on the bunker. Shortly afterward, eight people were charged with facilitating two hundred and forty-nine thousand criminal transactions. Much like familiar e-commerce platforms, dark web marketplaces are organized to offer a smooth buying and selling experience.

However, they aren’t visible on the open internet and require specialized browsers like Tor to access. This added layer of encryption masks users’ locations, making it nearly impossible to trace activity back to individuals. Following Silk Road’s closure, AlphaBay emerged in 2014, introducing advanced security features such as two-factor authentication and multi-signature escrow services to improve vendor credibility. At its peak, AlphaBay had over 400,000 users and facilitated transactions exceeding $1 billion. Transactions within dark markets predominantly involve cryptocurrencies like Bitcoin, Monero, or Ethereum. These digital currencies provide a degree of anonymity, as transactions are recorded on a public ledger but do not directly link users to their real-world identities.
Does The Darknet Still Exist?
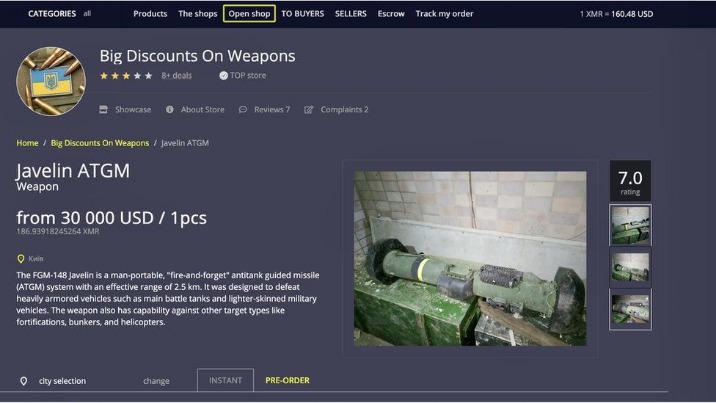
The dark web is home to many online marketplaces, offering everything from digital goods to rare items. If you’re searching for a reliable dark web marketplace, We The North Market provides secure transactions, encrypted communications, and a low 5% vendor fee. In this guide, we’ll break down the top dark web markets and how to stay safe while using them.
It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data. The dark web market changes all the time, but some dark web marketplaces have made a name for themselves as the biggest and busiest spots. These sites attract thousands of users every day, offering all kinds of illegal goods that keep the underground trade going.
How To Access The Dark Web: Step-by-Step Tutorial (and A Few Words Of Caution)
The legality depends on your activities and your country’s specific laws regarding darknet use. Silk Road was once the most well-known dark web marketplace, but after its shutdown, many new markets took its place. Today, buyers and vendors look for reliable alternatives that offer security, escrow protection, and a strong vendor community.
About SecurityWeek
That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia. Browsers with the appropriate proxy can reach these sites, but others can’t. The terms “deep web” and “dark web” are sometimes used interchangeably, but they are not the same. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google.
What Types Of Marketplaces Can You Find On The Dark Web?

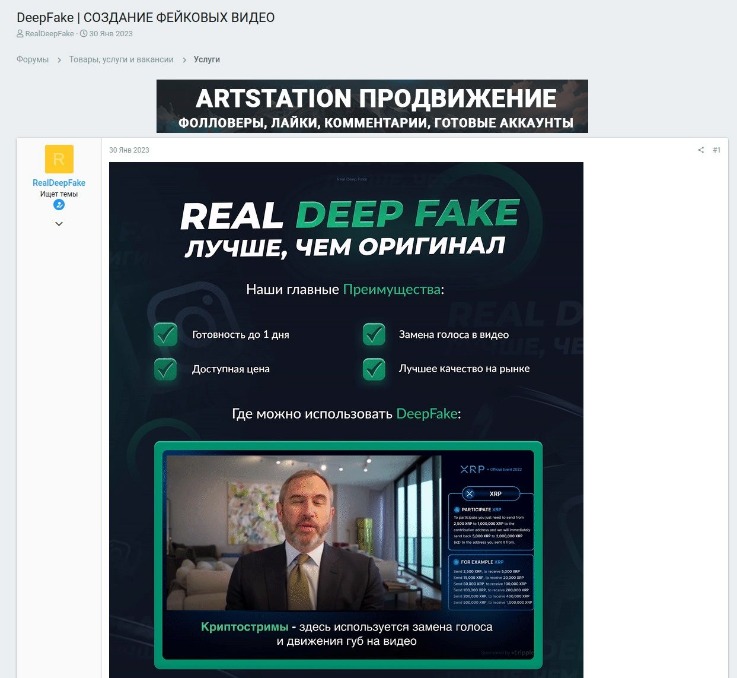
It lowers the initial threshold of expertise required by would-be cybercriminals. They lure crypto users to scam sites and Telegram bots under various guises, and add crypto-stealing functionality to infostealers and banking Trojans. With the price of Bitcoin setting record after record, the popularity of drainers specifically designed to steal cryptocurrency tokens from victims’ wallets is likely to persist in the coming year. While some of this growth may be attributed to the reposting or combining of older leaks, cybercriminals are clearly interested in distributing leaked data – whether new, old, or even fake. Consequently, in 2025, we are likely to witness not only a rise in company data hacks and leaks through contractors, but also an overall increase in data breaches.
Beyond legal requirements, businesses bear an ethical responsibility to safeguard the sensitive data of their customers and employees. A failure to secure this information not only exposes stakeholders to risks but also undermines trust in the organization. Implementing a comprehensive security gap assessment ensures businesses can proactively identify vulnerabilities and uphold their ethical obligations. The first ever DNM — called Silk Road — was started in 2011 by U.S. citizen Ross Ulbricht. While it included some innocuous listings such as health supplements, the majority of vendors and most of the sales were related to illicit drugs.

Compared to its predecessors, Archetyp enforced enhanced security expectations from its users. These included an advanced encryption program known as “Pretty Good Privacy” and a cryptocurrency called Monero. Unlike Bitcoin, which records every payment on a public ledger, Monero conceals all transaction details by default, which makes them nearly impossible to trace. Last week, one of the dark web’s most prominent drug marketplaces—Archetyp—was shut down in an international, multi-agency law enforcement operation following years of investigations.
- Individuals are also at risk, as their personal information can be exploited for identity theft or sold multiple times over.
- A vast number of URLs have domain endings such as “.onion”, which means that the URLs are only accessible by Tor users.
- If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer.
- TRM provides blockchain intelligence to help financial institutions, cryptocurrency businesses, and public agencies detect, investigate, and manage crypto-related fraud and financial crime.
- Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures.
Fifth, we consider the lifetime of each entity i at time t, defined as the time interval between the first and the last transaction performed by the entity until time t, denoted by \(\ell _i(t)\). This feature is satisfied when \(\ell _i(t) \ge L\), where L is the fixed value of minimum lifetime. From 2012 to 2016, the largest component of S2S network continuously grows in number of nodes and connections, as shown in Fig. Then, during 2017 and 2018, it shows the structural change due to operation Bayonet, when it shrinks.
Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. I2P can only be used to access hidden sites that are only available on the I2P network. All of the above is why I strongly recommend using the dark web not for access to iffy or outright illegal trading of goods and services, but instead to gain access to information you might normally be blocked from. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web. As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor.
For example, non-compliance can result in fines of up to 4% of an organization’s global annual revenue. Additionally, where non-compliant cash out points are facilitating the movement of illicit funds from DNMs, regulators and law enforcement may take action to disrupt activity at the cash out point itself. For example, concurrent with the takedown of Hydra was the sanctioning of Garantex, the Moscow-based exchange that made multiple transactions with Hydra-linked addresses. On top of that, undercover operations are a key strategy that’s being used, with agents posing as buyers or sellers to infiltrate these markets. The field of digital forensics also plays an important role since it helps investigations trace digital footprints back to their sources. Undercover operations are also vital for these operations, with agents posing as buyers or sellers to infiltrate these markets.