
In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. The dark web marketplaces are mainly defined into two categories. The last item on our dark web websites list is Google Feud or rather its evil twin. For those of you unfamiliar with this, G-Feud is a clear web game where you have to guess the answers to some random or topic-related search strings. For instance, if you choose a topic (e.g. food), G-Feud will give you a string such as “can I eat…?
Awazon Market
To contribute a tip, join the community, which can be done anonymously through an approved onion link. The site is strongly resistant to hackers and encrypts your data in transit as well as the rest. Since you cannot access a library of dark web links using the regular Internet, you can check out platforms dedicated to indexing these sites, like The Hidden Wiki. With NordVPN’s double VPN feature, your traffic is routed through two servers for double encryption. It also includes a dark web monitoring feature that crawls the dark web and alerts you if your details show up anywhere.
Page Version Status
Sci-Hub has nothing to do with science-fiction literature, but with science itself. The first website on our list is, allegedly, the largest repositories of scientific papers on the dark web. In other words, it’s the dark web’s version of ScienceDirect.

The platform also cares about its users and uses PGP encryption and two-factor authentication to secure their data and communication. Like other marketplaces, ASAP Market also requires you to register for an account. The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption. The layers of encryption hide your data and activity from snooping eyes. Accessing any darknet marketplace is dangerous because it is known to be a hub for illegal trade. In addition, several fake websites impersonate the famous dark net marketplace to obtain your financial and personal information and use it for malicious purposes.
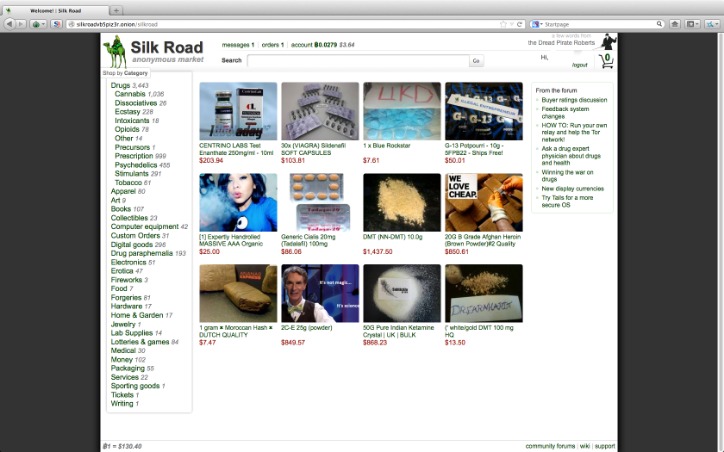
If you’re after secure email, look for the Proton Mail service. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. The story of dark web marketplaces kicks off with Silk Road, launched in 2011. It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.
The Cyber Express News

Onion services related to crypto include privacy wallets and block explorers. While legal, these tools spark debate because criminals also use them. Directories once acted as the main gateways to the dark web.
In the early 2000s, the project became public as Tor, short for The Onion Router. Nonprofit groups, academics, and privacy advocates joined the effort. Tor quickly grew into a global network of thousands of relays, run by volunteers around the world. Its mission shifted beyond military needs to protecting everyday users, journalists, and activists. It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself. Sections of the dark web are often closed down too, as part of police operations.
Do I Need A VPN If I Use Tor?
Accessing them through .onion domains adds another layer of anonymity. Milestones include the rise and fall of famous markets like Silk Road in 2011, which drew public attention to the dark web. At the same time, legitimate organizations such as ProPublica and the BBC launched their own onion sites, proving that the technology was not only for underground use.
Share This Article
No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged. Everything you find on the dark web is not necessarily illegal. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web.
BBC News In Your Language
You can even use a secure email provider or a burner email address whenever you visit the dark web. Tor2door Market is among the largest dark net shops you must visit in 2025 if you’ve decided to visit such sites. On average, the marketplace consists of more than 11,000 items and 1000 vendors. In April 2016, its APIs were compromised, resulting in stolen messages. But since its relaunch, the developers are focusing more on operational security and ensuring that users can have a good experience on this site. The website looks organized and has a clean, sleek, easy-to-use UI.
Report It To The Authorities (if It’s Safe To Do So)
In the hidden web, victims usually have no way to recover losses. Staying safe requires skepticism and verifying every address before trusting it. Look for signs of credibility, such as frequent updates, strong community references, and transparent moderation. The best approach is to confirm any onion address with multiple trusted sources before visiting.
- Scammers exploit outages by releasing fake versions of popular sites.
- It enhances buyer transparency by importing vendor feedback with PGP proof.
- Regularly update Tor Browser, VPN software, and operating systems to patch new vulnerabilities.
- The story of onion services begins in the 1990s, when researchers explored new ways to protect online communications.
- Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web.
- Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace.
Outdated software is one of the easiest ways attackers compromise devices. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. However, it’s much harder to get at the people who are doing the uploading and downloading. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. Open up Tor, and you won’t suddenly see the dark web staring back at you.
By treating each onion site with caution, you can explore responsibly without exposing yourself to unnecessary risks. Operators move servers, update security, or respond to attacks. Because of this, a domain that worked yesterday may fail today. Regularly update Tor Browser, VPN software, and operating systems to patch new vulnerabilities. Limit the number of add-ons or external tools that could create leaks. Treat every download with suspicion, and verify links through multiple sources before visiting.
It’s maintained by a volunteer-run collective from the USA that protects the platform from malicious attacks and pledges to support social justice and progressive causes. Riseup’s secure email and chat help individuals communicate without fear of surveillance or data interception. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. If you only want to mask your IP address and don’t need to access the dark web, then going online with a VPN is much easier and faster than using Tor. Activists, whistle blowers, and journalists also use the dark web to communicate securely with sources and news organizations. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts.
Even files that look harmless, like PDFs or images, may carry hidden threats. The safest approach is to assume every unverified link could be hostile until proven otherwise. Others provide encrypted vaults accessible only through Tor.



