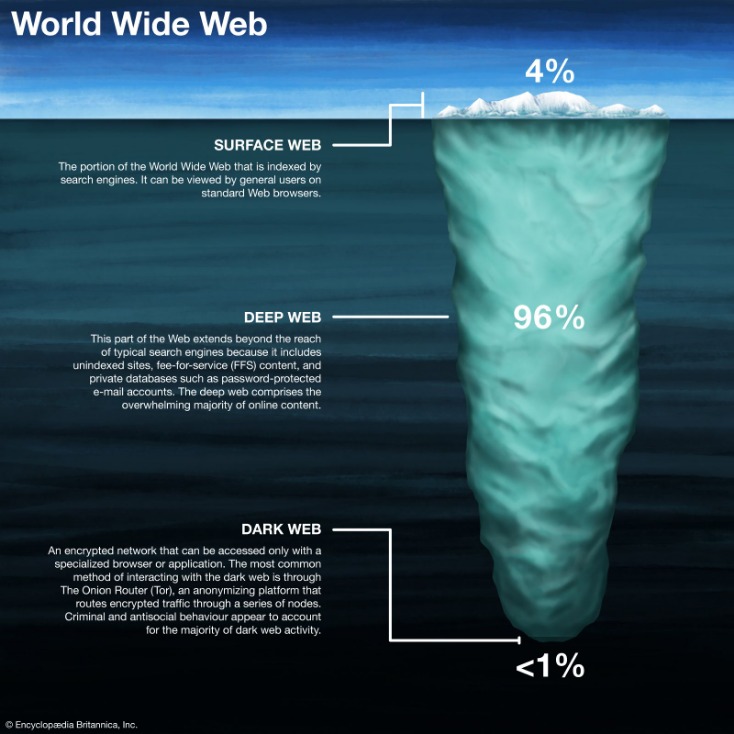
Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
Private Internet Access

So, instead of “facebook.com”, the URL can look like “12ls834mfdg8.onion”. AlphaBay was relaunched by DeSnake in August 2021 with a new design but with the same admin as before and is once again planning to become the biggest darknet market in history. If you’re having trouble opening a specific onion link, or the overall Tor speed is slow, we have detailed tips on how to make Tor faster. The website has received six Pulitzer Prizes for its grassroots-based journalism. Accessing it through an onion link is much more convenient if you’re unable to directly view it on your screen.
Dangerous Software
The very first of these marketplaces to pair the darknet with Bitcoin was the Silk Road. Over the next two years, the Silk Road set the standard for darknet marketplaces. By the time it was shut down in October 2013 and Ross Ulbricht arrested, the site had traded an estimated $183 million worth of goods and services.
Types Of Dark Web Sites (and What Really Goes On There)
“These guys have made at least 50 bitcoins nearly $23,000 on this,” said Chris Monteiro, an independent researcher who has been following the site. Along with a partner, he has also hacked into Besa Mafia and is still collecting messages. Monteiro said he wasn’t behind the dump of messages and other site data. The point of the site is, of course, to get people to hand over their bitcoins.
- We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch.
- Two of the leaked files, in .CSV format, contains 38 hit orders and nearly 3,000 personal messages sent between budding customers and the website’s administrators.
- Quite possibly the strangest murder-for-hire Deep Web site is Assassination Market, which bills itself as a system for crowdfunding assassinations.
- You can broker your illegal transaction and a third broker can handle this for you.
- Chris’ target was an assassination market nestled on the ‘dark net’, a slice of the Internet where nobody knows who you are, and nobody knows where you go.
In practice, we found very little use of VPN Over Tor and saw no significant advantages. During this process, your ISP can still see that you’re using Tor because the entry node is now fully visible. Not to mention the entry node will see your IP address, so if it’s compromised, a hacker would be able to get a hold of it. More importantly, even the VPN service will now see what you’re doing inside Tor. Just for laughs and giggles, we visited this random pug’s ultimate guide to the dark web. You’ll notice that some websites’ loading times are longer when using Tor.
How To Find Active Onion Dark Web Sites (And Why You Might Want To)
While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs.
Remember to access the Deep web links in a safe and anonymous way. Yippy is a search engine that started in 2009, since then it has evolved. To become a leading provider of business learning and knowledge for all types of data users and consumers. The search engine provides several special features beyond the original word. These include weather forecasts, maps, calculations and Boolean operations as inclusion or alternatives among others. Always the wikipedian, Monteiro had begun to structure his trove of Besa Mafia-related information in a password-protected BesaWiki.
Our first priority was figuring out how much danger the targets were really in. And what the messages revealed was that there were no real hitmen. Instead, the administrators would make up excuses for why the murder hadn’t been carried out—the hitman got lost, or the victim was too well protected—before the customer finally gave up. The Tor browser is a modified Mozilla Firefox browser with numerous integrated scripts and add-ons to protect your privacy while browsing onion sites. The Tor network is a series of interconnected nodes that allow anonymous internet use. Tor stands for “The Onion Router,” while sites hosted on the service carry the “.onion” top-level domain suffix.

The New York Times operates one of the biggest news sites on the Tor network, letting users access its regular news coverage with increased privacy and security. The onion site is especially beneficial for people in regions with heavy censorship or restricted access to media. Pipl is designed as a people search engine that searches global identification information to enable organizations to make connections that others cannot. Ahmia is one of the search engines intended to get into the Tor browser. It filters out dangerous sites and has been instrumental in raising awareness about sites that attempt to trick users.
Connecting To A VPN Server
It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together.
Marketing Hub
- “I initially thought it would be gangland, drugs deals gone wrong, that kind of thing,” Miller reveals.
- More importantly, even the VPN service will now see what you’re doing inside Tor.
- For me, this is only over when I’ve actioned the remainder of Kill List.
- Customers submitted the details of the person they wanted killed and the method they preferred – for instance, a hit that looked like an accident would be more expensive.
- People have been organizing illicit trades via the Internet since the 1970s.
Gizmodo may earn a commission when you buy through links on the site. Tor supports a few systems only – Windows, macOS, Linux, and Android. IOS is the only exception, leaving iPhone and iPad users without the option to go to this part of the internet.
Take control of your digital security with an exclusive demo of our powerful threat management platform. For businesses and individuals alike, understanding these threats is the first step in securing their digital assets. However, combating dark web risks requires more than just awareness—it demands proactive and comprehensive protection. As you can imagine, the dark web has some forums filled with the types of characters who are best avoided. However, one of the less obscene discussion sites is Raddle, named and styled somewhat in the style of Reddit. Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship.
A Tor browser, which routes users’ information through a system of nodes around the world rendering people using the service effectively anonymous, is required to obtain access. However, from there, finding someone with a certain moral flexibility is as easy as searching “assassin” or “hitman” on one of the many Deep Web forums or search engines. Additionally, there has never been a murder definitively attributed to dark-web hitmen. While illegal activities do occur on the dark web, we believe that most hitmen-for-hire sites are scams, designed to steal thousands in bitcoins from unsuspecting users.
This lack of accountability poses a significant risk to society, as it allows criminal activities to flourish in the shadows. Of course hitmen do exist and there are reports of dark-web related murders, it’s just that these murder-for-hire eCommerce style sites smell so much like scams. If you manage to not expose your private information and avoid illicit activities, you can be sure everything will be okay. Using NordVPN or even ExpressVPN or PIA seems to be beneficial for many users. Such providers offer strong encryption and don’t store logs, ensuring all online footsteps are completely masked.
ZeroBin is a minimalist paste-bin tool that allows users to share text securely and privately on the Tor network. Riseup is available on the surface web, but its presence on the Tor network extends its privacy benefits by letting you use its services without exposing their real-world identities. You can access encrypted email services through the onion site without getting tracked.
Safe E-mail Services
Never share personal information, avoid clicking suspicious links, and consider using additional layers of privacy like a VPN. The dark web offers privacy and anonymity, but that also attracts malicious actors. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on. Before clicking any of the dark web links below, you’ll need to get the Tor Browser (also called the Onion Browser) or another service that provides dark web access, such as the Brave browser.