It enhances buyer transparency by importing vendor feedback with PGP proof. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected.
II Security And Anonymity On The Dark Web
So, instead of checking individual libraries for the needed resources, you can browse and access those from one search box. Be it books, magazines, articles, photos, ebooks, audiobooks, CDs, DVDs, maps, records, or theses, you can find all these on this search engine. Currently, it compiles all the crucial links for different sectors, including computer science, engineering, education, natural sciences, law, arts, society, and culture.
Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address.
As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring. Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats. At the end of the day, searching on the Deep Web should be done cautiously. Some Deep Web search engines discussed here are perfectly okay to explore, but once you get into the Tor world, your online guard should be up.
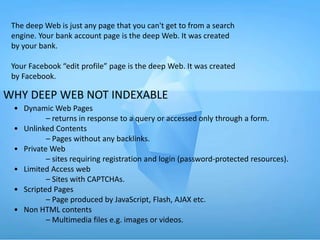
Non-indexed Content
Do note that accessing the onion search results on DDG will require you to download the Tor browser. It’s recommended to open the search engine site on Tor itself so a DDG onion link is generated. From the main search page, you can link through to sites of specific institutions and even tribal governments, accessing all kinds of records from birth and death certificates to old legal information.
How To Hide IP Address In 2025 (A Comprehensive Guide)
The keyword in that example is “onioname,” which is right at the start of the .onion link. With a readable site name like that, people will know what to expect when they click on the link. This is a blog with cybersecurity tips created by the Electronic Frontier Foundation (EFF), a popular non-profit that specializes in digital privacy. The blog contains tons of useful guides about how you can avoid online surveillance.

White House Market
If you’ve one for secrets and history, the IIT Underground site is a site run by an individual who has taken upon himself to explore the hidden tunnels under the Illinois Institute of Technology. The site hosts a number of photos and facts regarding the Tunnels, documented first-hand after visiting the Tunnels. It has categories such as “Roofs” “Maps” “Tunnels” etc which help users navigate around the site and reach areas of interest. If you are new to Tor network, check out this guide to know how to access Tor websites. To solve this, we compiled a list of nearly 60 working, legal Tor links.
I Legal And Ethical Considerations

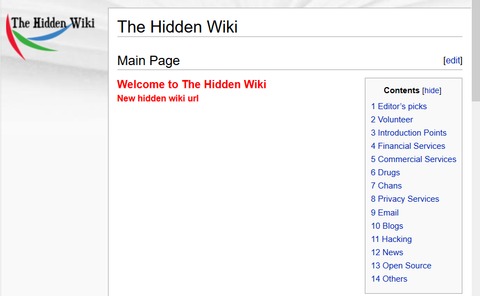
It emphasizes anonymity while providing familiar social media features. Some content can be unmoderated, though, so it’s worthwhile to be careful while using this platform. The Hidden Wiki is a comprehensive starting point for exploring verified dark web links. Unlike many imitators, this is the official Hidden Wiki that maintains a curated directory of legitimate .onion services. During my testing, I found its categorized index particularly helpful for discovering trustworthy sites across various topics.

O Que É A Dark Web? Como Se Proteger Visitando Sites onion
- Search engines and corporate websites might be OK, but even a popular Tor website like Hidden Wiki can show illegal deep web links that jeopardize your online safety.
- What’s more, you should always use a VPN (like ExpressVPN) with Tor to protect yourself from IP leaks.
- The process costs a fee, but unlike other “tumbler” or “mixing” services, there is no risk that Wasabi or any of its users could scam you out of your coins.
- Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved.
- While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored.
This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites. Using the ProtonMail .onion site offers security and privacy advantages. Moreover, the company also uses HTTPS and SSL encryption on the Onion site for extra protection. This makes it even harder for third parties to see your email traffic. ProtonMail is a Swiss-based email service that is very easy to use.
Although the social application is known for collecting data on its platform, it does not like sharing the information with others. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information. There are multiple search engines on the dark web that can help you find what you’re looking for.
Cyble Strato Cloud Security
Lets users report abusive or unacceptable links which further establishes the fact of it being a legal Tor link. PasterNinja is the Darknet Pastebin, or in other words one of the many legal Tor links alike Pastebin on the Tor network. It’s heavily encrypted client-side making sure the server can never read the information pasted on the platform, the encryption key is always saved on the user’s system and not online or on the server.
DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia. You don’t need special tools or a special browser like you need to access the dark web (more about that later). Anyone can access the deep web by using specialized search engines, dedicated web directories, and other sources that can help you find the data or information. The Silk Road was a famous dark web marketplace where users could buy and sell goods and services anonymously. All the payments were made through cryptocurrency, further enhancing marketplace anonymity.
Indeed, some began life on the clear web before migrating to the dark web to evade surveillance or censorship. Forums cover the breadth of criminal activity but these examples show there is a particularly thriving community of cybercriminals sharing information, tutorials, access, and exploits. As long as there’s a demand for the ability to privately browse the internet and, more importantly, host websites anonymously, the deep web will exist. Due to its decentralized structure, there is no real way to “shut down” the deep net, just like you can’t really shut down the regular internet. Another problem with this system is that there’s increasing evidence that law enforcement agencies — such as the FBI — run and operate large number of exit nodes.



